FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
FEDERAL SUPPLY SERVICE Federal Network Systems LLC - Verizon
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
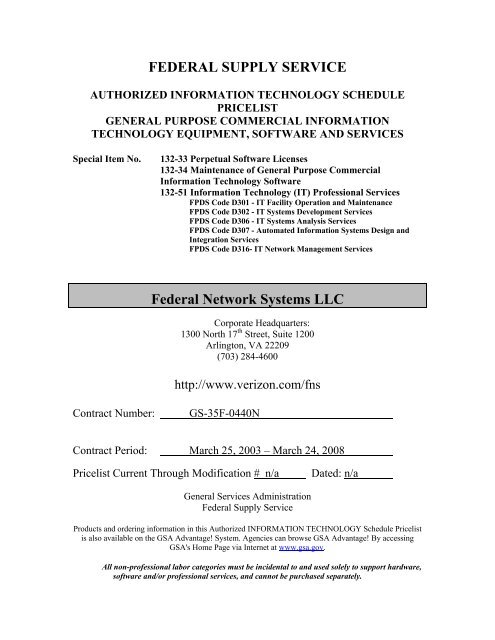
<strong>FEDERAL</strong> <strong>SUPPLY</strong> <strong>SERVICE</strong><br />
AUTHORIZED INFORMATION TECHNOLOGY SCHEDULE<br />
PRICELIST<br />
GENERAL PURPOSE COMMERCIAL INFORMATION<br />
TECHNOLOGY EQUIPMENT, SOFTWARE AND <strong>SERVICE</strong>S<br />
Special Item No.<br />
132-33 Perpetual Software Licenses<br />
132-34 Maintenance of General Purpose Commercial<br />
Information Technology Software<br />
132-51 Information Technology (IT) Professional Services<br />
FPDS Code D301 - IT Facility Operation and Maintenance<br />
FPDS Code D302 - IT <strong>Systems</strong> Development Services<br />
FPDS Code D306 - IT <strong>Systems</strong> Analysis Services<br />
FPDS Code D307 - Automated Information <strong>Systems</strong> Design and<br />
Integration Services<br />
FPDS Code D316- IT <strong>Network</strong> Management Services<br />
<strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong><br />
Corporate Headquarters:<br />
1300 North 17 th Street, Suite 1200<br />
Arlington, VA 22209<br />
(703) 284-4600<br />
http://www.verizon.com/fns<br />
Contract Number:<br />
GS-35F-0440N<br />
Contract Period: March 25, 2003 – March 24, 2008<br />
Pricelist Current Through Modification # n/a<br />
Dated: n/a<br />
General Services Administration<br />
<strong>Federal</strong> Supply Service<br />
Products and ordering information in this Authorized INFORMATION TECHNOLOGY Schedule Pricelist<br />
is also available on the GSA Advantage! System. Agencies can browse GSA Advantage! By accessing<br />
GSA's Home Page via Internet at www.gsa.gov.<br />
All non-professional labor categories must be incidental to and used solely to support hardware,<br />
software and/or professional services, and cannot be purchased separately.
TABLE OF CONTENTS<br />
INFORMATION FOR ORDERING OFFICES..............................................................................................2<br />
TERMS AND CONDITIONS APPLICABLE TO PERPETUAL SOFTWARE LICENSES (SPECIAL<br />
ITEM NUMBER 132-33) AND MAINTENANCE OF GENERAL PURPOSE COMMERCIAL<br />
INFORMATION TECHNOLOGY SOFTWARE (SPECIAL ITEM NUMBER 132-34)............................10<br />
SOFTWARE PRODUCT DESCRIPTION ...................................................................................................12<br />
TERMS AND CONDITIONS APPLICABLE TO INFORMATION TECHNOLOGY (IT)<br />
PROFESSIONAL <strong>SERVICE</strong>S (SPECIAL ITEM NUMBER 132-51) .........................................................15<br />
IT <strong>SERVICE</strong>S DESCRIPTIONS ..................................................................................................................19<br />
IT LABOR CATEGORY DESCRIPTIONS .................................................................................................30<br />
IT <strong>SERVICE</strong>S HOURLY RATES ................................................................................................................56
INFORMATION FOR ORDERING OFFICES<br />
APPLICABLE TO ALL SPECIAL ITEM NUMBERS<br />
SPECIAL NOTICE TO AGENCIES: Small Business Participation<br />
SBA strongly supports the participation of small business concerns in the <strong>Federal</strong> Supply Schedules<br />
Program. To enhance Small Business Participation SBA policy allows agencies to include in their<br />
procurement base and goals, the dollar value of orders expected to be placed against the <strong>Federal</strong> Supply<br />
Schedules, and to report accomplishments against these goals.<br />
For orders exceeding the micropurchase threshold, FAR 8.404 requires agencies to consider the<br />
catalogs/pricelists of at least three schedule contractors or consider reasonably available information by<br />
using the GSA Advantage! on-line shopping service (www.fss.gsa.gov). The catalogs/pricelists, GSA<br />
Advantage! and the <strong>Federal</strong> Supply Service Home Page (www.fss.gsa.gov) contain information on a<br />
broad array of products and services offered by small business concerns.<br />
This information should be used as a tool to assist ordering activities in meeting or exceeding established<br />
small business goals. It should also be used as a tool to assist in including small, small disadvantaged, and<br />
women-owned small businesses among those considered when selecting pricelists for a best value<br />
determination.<br />
For orders exceeding the micropurchase threshold, customers are to give preference to small business<br />
concerns when two or more items at the same delivered price will satisfy their requirement.<br />
1. Geographic Scope of Contract:<br />
The geographic scope of the contract is the 48 contiguous states, Hawaii, Alaska, and the District of<br />
Columbia<br />
2. Contractor's Ordering Address and Payment Information:<br />
Ordering Address:<br />
Tony Traina<br />
1300 North 17 th Street, Suite 1200<br />
Arlington, VA 22209<br />
Payment Address:<br />
<strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong><br />
C/O Wachovia Bank<br />
P.O. Box 101761<br />
Atlanta, GA 30392-1761<br />
Account # 1861-087125<br />
Contractors are required to accept the Government purchase card for payments equal to or less than the<br />
micro-purchase threshold for oral or written delivery orders. Government purchase cards will be acceptable<br />
for payment above the micro-purchase threshold. In addition, bank account information for wire transfer<br />
payments will be shown on the invoice. The following telephone number(s) can be used by ordering<br />
agencies to obtain technical and/or ordering assistance:<br />
For ordering assistance: (703) 284-4600
3. LIABILITY FOR INJURY OR DAMAGE<br />
The Contractor shall not be liable for any injury to Government personnel or damage to Government<br />
property arising from the use of equipment maintained by the Contractor, unless such injury or damage is<br />
due to the fault or negligence of the Contractor.<br />
4. Statistical Data for Government Ordering Office Completion of Standard Form 279:<br />
Block 9: G. Order/Modification Under <strong>Federal</strong> Schedule<br />
Block 16: Data Universal Numbering System (DUNS) Number: 13-342-4023<br />
Block 30: Type of Contractor - C. Large Business<br />
Block 31: Woman-Owned Small Business – No<br />
Block 36: Contractor's Taxpayer Identification Number (TIN): 04-350-6726<br />
4a. CAGE Code: 1PTG2<br />
4b. Contractor has with the Central Contractor Registration Database.<br />
5. FOB Destination<br />
6. DELIVERY SCHEDULE<br />
a. TIME OF DELIVERY: The Contractor shall deliver to destination within the number of calendar<br />
days after receipt of order (ARO), as set forth below:<br />
SPECIAL ITEM NUMBER<br />
DELIVERY TIME (Days ARO)<br />
132-51 As mutually agreed by the ordering agency and FNS<br />
132-33, 132-34 30 Days<br />
b. URGENT REQUIREMENTS: When the <strong>Federal</strong> Supply Schedule contract delivery period does<br />
not meet the bona fide urgent delivery requirements of an ordering agency, agencies are encouraged, if time<br />
permits, to contact the Contractor for the purpose of obtaining accelerated delivery. The Contractor shall<br />
reply to the inquiry within three (3) workdays after receipt. (Telephonic replies shall be confirmed by the<br />
Contractor in writing.) If the Contractor offers an accelerated delivery time acceptable to the ordering<br />
agency, any order(s) placed pursuant to the agreed upon accelerated delivery time frame shall be delivered<br />
within this shorter delivery time and in accordance with all other terms and conditions of the contract.<br />
7. Discounts: Prices shown are NET Prices; Basic Discounts have been deducted.<br />
a. Prompt Payment: net thirty (30) days from receipt of invoice or date of acceptance,<br />
whichever is later<br />
b. Quantity: None<br />
c. Dollar Volume: None<br />
d. Government Educational Institutions: Government Educational institutions are offered<br />
the same discounts as all other Government customers.<br />
e. Other: None
8. Trade Agreements Act of 1979, as amended:<br />
All items are U.S. made end products, designated country end products, Caribbean Basin country end<br />
products, Canadian end products, or Mexican end products as defined in the Trade Agreements Act of<br />
1979, as amended.<br />
9. Statement Concerning Availability of Export Packing:<br />
NetFacade is not available outside of the United States<br />
10. Small Requirements: The minimum dollar value of orders to be issued is $100.<br />
11. Maximum Order<br />
a. The Maximum Order value for the following Special Item Numbers (SINs) is $500,000:<br />
Special Item Number 132-33 - Perpetual Software Licenses<br />
Special Item Number 132-51 - Information Technology (IT) Professional Services<br />
Note: Maximum Orders do not apply to Special Item Number 132-34 Maintenance of Software.<br />
12. USE OF <strong>FEDERAL</strong> <strong>SUPPLY</strong> <strong>SERVICE</strong> INFORMATION TECHNOLOGY SCHEDULE<br />
CONTRACTS. In accordance with FAR 8.404:<br />
[NOTE: Special ordering procedures have been established for Special Item Numbers (SINs) 132-51<br />
IT Professional Services and 132-52 EC Services; refer to the terms and conditions for those SINs.]<br />
Orders placed pursuant to a Multiple Award Schedule (MAS), using the procedures in FAR 8.404, are<br />
considered to be issued pursuant to full and open competition. Therefore, when placing orders under<br />
<strong>Federal</strong> Supply Schedules, ordering offices need not seek further competition, synopsize the requirement,<br />
make a separate determination of fair and reasonable pricing, or consider small business set-asides in<br />
accordance with subpart 19.5. GSA has already determined the prices of items under schedule contracts to<br />
be fair and reasonable. By placing an order against a schedule using the procedures outlined below, the<br />
ordering office has concluded that the order represents the best value and results in the lowest overall cost<br />
alternative (considering price, special features, administrative costs, etc.) to meet the Government’s needs.<br />
a. Orders placed at or below the micro-purchase threshold. Ordering offices can place orders at or<br />
below the micro-purchase threshold with any <strong>Federal</strong> Supply Schedule Contractor.<br />
b. Orders exceeding the micro-purchase threshold but not exceeding the maximum order threshold.<br />
Orders should be placed with the Schedule Contractor that can provide the supply or service that represents<br />
the best value. Before placing an order, ordering offices should consider reasonably available information<br />
about the supply or service offered under MAS contracts by using the “GSA Advantage!” on-line shopping<br />
service, or by reviewing the catalogs/pricelists of at least three Schedule Contractors and selecting the<br />
delivery and other options available under the schedule that meets the agency’s needs. In selecting the<br />
supply or service representing the best value, the ordering office may consider --<br />
(1) Special features of the supply or service that are required in effective program<br />
performance and that are not provided by a comparable supply or service;<br />
(2) Trade-in considerations;<br />
(3) Probable life of the item selected as compared with that of a comparable item;<br />
(4) Warranty considerations;<br />
(5) Maintenance availability;
(6) Past performance; and<br />
(7) Environmental and energy efficiency considerations.<br />
c. Orders exceeding the maximum order threshold. Each schedule contract has an established<br />
maximum order threshold. This threshold represents the point where it is advantageous for the ordering<br />
office to seek a price reduction. In addition to following the procedures in paragraph b, above, and before<br />
placing an order that exceeds the maximum order threshold, ordering offices shall --<br />
Review additional Schedule Contractors’<br />
(1) Catalogs/pricelists or use the “GSA Advantage!” on-line shopping service;<br />
(2) Based upon the initial evaluation, generally seek price reductions from the Schedule<br />
Contractor(s) appearing to provide the best value (considering price and other factors); and<br />
(3) After price reductions have been sought, place the order with the Schedule Contractor<br />
that provides the best value and results in the lowest overall cost alternative. If further price<br />
reductions are not offered, an order may still be placed, if the ordering office determines that it is<br />
appropriate.<br />
NOTE: For orders exceeding the maximum order threshold, the Contractor may:<br />
(1) Offer a new lower price for this requirement (the Price Reductions clause is not<br />
applicable to orders placed over the maximum order in FAR 52.216-19 Order Limitations);<br />
(2) Offer the lowest price available under the contract; or<br />
(3) Decline the order (orders must be returned in accordance with FAR 52.216-19).<br />
d. Blanket purchase agreements (BPAs). The establishment of <strong>Federal</strong> Supply Schedule BPAs is<br />
permitted when following the ordering procedures in FAR 8.404. All schedule contracts contain BPA<br />
provisions. Ordering offices may use BPAs to establish accounts with Contractors to fill recurring<br />
requirements. BPAs should address the frequency of ordering and invoicing, discounts, and delivery<br />
locations and times.<br />
e. Price reductions. In addition to the circumstances outlined in paragraph c, above, there may be<br />
instances when ordering offices will find it advantageous to request a price reduction. For example, when<br />
the ordering office finds a schedule supply or service elsewhere at a lower price or when a BPA is being<br />
established to fill recurring requirements, requesting a price reduction could be advantageous. The<br />
potential volume of orders under these agreements, regardless of the size of the individual order, may offer<br />
the ordering office the opportunity to secure greater discounts. Schedule Contractors are not required to<br />
pass on to all schedule users a price reduction extended only to an individual agency for a specific order.<br />
f. Small business. For orders exceeding the micro-purchase threshold, ordering offices should give<br />
preference to the items of small business concerns when two or more items at the same delivered price will<br />
satisfy the requirement.<br />
g. Documentation. Orders should be documented, at a minimum, by identifying the Contractor the<br />
item was purchased from, the item purchased, and the amount paid. If an agency requirement in excess of<br />
the micro-purchase threshold is defined so as to require a particular brand name, product, or feature of a<br />
product peculiar to one manufacturer, thereby precluding consideration of a product manufactured by<br />
another company, the ordering office shall include an explanation in the file as to why the particular brand<br />
name, product, or feature is essential to satisfy the agency’s needs.<br />
13. <strong>FEDERAL</strong> INFORMATION TECHNOLOGY/TELECOMMUNICATION STANDARDS<br />
REQUIREMENTS: <strong>Federal</strong> departments and agencies acquiring products from this Schedule must comply<br />
with the provisions of the <strong>Federal</strong> Standards Program, as appropriate (reference: NIST <strong>Federal</strong> Standards<br />
Index). Inquiries to determine whether or not specific products listed herein comply with <strong>Federal</strong><br />
Information Processing Standards (FIPS) or <strong>Federal</strong> Telecommunication Standards (FED-STDS), which<br />
are cited by ordering offices, shall be responded to promptly by the Contractor.
13.1 <strong>FEDERAL</strong> INFORMATION PROCESSING STANDARDS PUBLICATIONS (FIPS PUBS):<br />
Information Technology products under this Schedule that do not conform to <strong>Federal</strong> Information<br />
Processing Standards (FIPS) should not be acquired unless a waiver has been granted in accordance with<br />
the applicable "FIPS Publication." <strong>Federal</strong> Information Processing Standards Publications (FIPS PUBS)<br />
are issued by the U.S. Department of Commerce, National Institute of Standards and Technology (NIST),<br />
pursuant to National Security Act. Information concerning their availability and applicability should be<br />
obtained from the National Technical Information Service (NTIS), 5285 Port Royal Road, Springfield,<br />
Virginia 22161. FIPS PUBS include voluntary standards when these are adopted for <strong>Federal</strong> use.<br />
Individual orders for FIPS PUBS should be referred to the NTIS Sales Office, and orders for subscription<br />
service should be referred to the NTIS Subscription Officer, both at the above address, or telephone number<br />
(703) 487-4650.<br />
13.2 <strong>FEDERAL</strong> TELECOMMUNICATION STANDARDS (FED-STDS): Telecommunication<br />
products under this Schedule that do not conform to <strong>Federal</strong> Telecommunication Standards (FED-STDS)<br />
should not be acquired unless a waiver has been granted in accordance with the applicable "FED-STD."<br />
<strong>Federal</strong> Telecommunication Standards are issued by the U.S. Department of Commerce, National Institute<br />
of Standards and Technology (NIST), pursuant to National Security Act. Ordering information and<br />
information concerning the availability of FED-STDS should be obtained from the GSA, <strong>Federal</strong> Supply<br />
Service, Specification Section, 470 East L’Enfant Plaza, Suite 8100, SW, Washington, DC 20407,<br />
telephone number (202) 619-8925. Please include a self-addressed mailing label when requesting<br />
information by mail. Information concerning their applicability can be obtained by writing or calling the<br />
U.S. Department of Commerce, National Institute of Standards and Technology, Gaithersburg, MD 20899,<br />
telephone number (301) 975-2833.<br />
14. SECURITY REQUIREMENTS. In the event security requirements are necessary, the ordering<br />
activities may incorporate, in their delivery orders, a security clause in accordance with current laws,<br />
regulations, and individual agency policy; however, the burden of administering the security requirements<br />
shall be with the ordering agency. If any costs are incurred as a result of the inclusion of security<br />
requirements, such costs will not exceed ten percent (10%) or $100,000, of the total dollar value of the<br />
order, whichever is less.<br />
15. CONTRACT ADMINISTRATION FOR ORDERING OFFICES: Any ordering office, with<br />
respect to any one or more delivery orders placed by it under this contract, may exercise the same rights of<br />
termination as might the GSA Contracting Officer under provisions of FAR 52.212-4, paragraphs (l)<br />
Termination for the Government’s convenience, and (m) Termination for Cause (See C.1.).<br />
16. GSA Advantage!<br />
GSA Advantage! is an on-line, interactive electronic information and ordering system that provides on-line<br />
access to vendors' schedule prices with ordering information. GSA Advantage! will allow the user to<br />
perform various searches across all contracts including, but not limited to:<br />
(1) Manufacturer;<br />
(2) Manufacturer's Part Number; and<br />
(3) Product categories.<br />
Agencies can browse GSA Advantage! by accessing the Internet World Wide Web utilizing a browser (ex.:<br />
NetScape). The Internet address is http://www.fss.gsa.gov/.<br />
17. PURCHASE OF OPEN MARKET ITEMS<br />
NOTE: Open Market Items are also known as incidental items, noncontract items, non-Schedule items,<br />
and items not on a <strong>Federal</strong> Supply Schedule contract.<br />
For administrative convenience, an ordering office contracting officer may add items not on the <strong>Federal</strong><br />
Supply Multiple Award Schedule (MAS) -- referred to as open market items -- to a <strong>Federal</strong> Supply<br />
Schedule blanket purchase agreement (BPA) or an individual task or delivery order, only if --<br />
(1) All applicable acquisition regulations pertaining to the purchase of the items not on the<br />
<strong>Federal</strong> Supply Schedule have been followed (e.g., publicizing (Part 5), competition requirements
(Part 6), acquisition of commercial items (Part 12), contracting methods (Parts 13, 14, and 15),<br />
and small business programs (Part 19));<br />
(2) The ordering office contracting officer has determined the price for the items not on the<br />
<strong>Federal</strong> Supply Schedule is fair and reasonable;<br />
(3) The items are clearly labeled on the order as items not on the <strong>Federal</strong> Supply Schedule;<br />
and<br />
(4) All clauses applicable to items not on the <strong>Federal</strong> Supply Schedule are included in the<br />
order.<br />
18. CONTRACTOR COMMITMENTS, WARRANTIES AND REPRESENTATIONS<br />
a. For the purpose of this contract, commitments, warranties and representations include, in addition<br />
to those agreed to for the entire schedule contract:<br />
(1) Time of delivery/installation quotations for individual orders;<br />
(2) Technical representations and/or warranties of products concerning performance, total<br />
system performance and/or configuration, physical, design and/or functional characteristics and<br />
capabilities of a product/equipment/service/software package submitted in response to<br />
requirements which result in orders under this schedule contract.<br />
(3) Any representations and/or warranties concerning the products made in any literature,<br />
description, drawings and/or specifications furnished by the Contractor.<br />
b. The above is not intended to encompass items not currently covered by the GSA Schedule<br />
contract.<br />
19. OVERSEAS ACTIVITIES<br />
The terms and conditions of this contract shall apply to all orders for installation, maintenance and repair of<br />
equipment in areas listed in the pricelist outside the 48 contiguous states and the District of Columbia,<br />
except as indicated below:<br />
Upon request of the Contractor, the Government may provide the Contractor with logistics support, as<br />
available, in accordance with all applicable Government regulations. Such Government support will be<br />
provided on a reimbursable basis, and will only be provided to the Contractor's technical personnel whose<br />
services are exclusively required for the fulfillment of the terms and conditions of this contract.<br />
20. BLANKET PURCHASE AGREEMENTS (BPAs)<br />
<strong>Federal</strong> Acquisition Regulation (FAR) 13.303-1(a) defines Blanket Purchase Agreements (BPAs) as “…a<br />
simplified method of filling anticipated repetitive needs for supplies or services by establishing ‘charge<br />
accounts’ with qualified sources of supply.” The use of Blanket Purchase Agreements under the <strong>Federal</strong><br />
Supply Schedule Program is authorized in accordance with FAR 13.303-2(c)(3), which reads, in part, as<br />
follows:<br />
“BPAs may be established with <strong>Federal</strong> Supply Schedule Contractors, if not inconsistent with the terms of<br />
the applicable schedule contract.”<br />
<strong>Federal</strong> Supply Schedule contracts contain BPA provisions to enable schedule users to maximize their<br />
administrative and purchasing savings. This feature permits schedule users to set up “accounts” with<br />
Schedule Contractors to fill recurring requirements. These accounts establish a period for the BPA and<br />
generally address issues such as the frequency of ordering and invoicing, authorized callers, discounts,<br />
delivery locations and times. Agencies may qualify for the best quantity/volume discounts available under
the contract, based on the potential volume of business that may be generated through such an agreement,<br />
regardless of the size of the individual orders. In addition, agencies may be able to secure a discount higher<br />
than that available in the contract based on the aggregate volume of business possible under a BPA.<br />
Finally, Contractors may be open to a progressive type of discounting where the discount would increase<br />
once the sales accumulated under the BPA reach certain prescribed levels. Use of a BPA may be<br />
particularly useful with the new Maximum Order feature. See the Suggested Format, contained in this<br />
Schedule Pricelist, for customers to consider when using this purchasing tool.<br />
21. CONTRACTOR TEAM ARRANGEMENTS<br />
Contractors participating in contractor team arrangements must abide by all terms and conditions of their<br />
respective contracts. This includes compliance with Clauses 552.238-74, Contractor’s Reports of Sales and<br />
552.238-76, Industrial Funding Fee, i.e., each contractor (team member) must report sales and remit the IFF<br />
for all products and services provided under its individual contract.<br />
22. INSTALLATION, DEINSTALLATION, REINSTALLATION<br />
The Davis-Bacon Act (40 U.S.C. 276a-276a-7) provides that contracts in excess of $2,000 to which the<br />
United States or the District of Columbia is a party for construction, alteration, or repair (including painting<br />
and decorating) of public buildings or public works with the United States, shall contain a clause that no<br />
laborer or mechanic employed directly upon the site of the work shall received less than the prevailing<br />
wage rates as determined by the Secretary of Labor. The requirements of the Davis-Bacon Act do not<br />
apply if the construction work is incidental to the furnishing of supplies, equipment, or services. For<br />
example, the requirements do not apply to simple installation or alteration of a public building or public<br />
work that is incidental to furnishing supplies or equipment under a supply contract. However, if the<br />
construction, alteration or repair is segregable and exceeds $2,000, then the requirements of the Davis-<br />
Bacon Act applies.<br />
The requisitioning activity issuing the task order against this contract will be responsible for proper<br />
administration and enforcement of the <strong>Federal</strong> labor standards covered by the Davis-Bacon Act. The<br />
proper Davis-Bacon wage determination will be issued by the ordering activity at the time a request for<br />
quotations is made for applicable construction classified installation, deinstallation, and reinstallation<br />
services under SIN 132-8.<br />
23. SECTION 508 COMPLIANCE.<br />
If applicable, Section 508 compliance information on the supplies and services in this contract are available<br />
in Electronic and Information Technology (EIT) at the following:<br />
www.verizon.com/fns<br />
The EIT standard can be found at: www.Section508.gov/.<br />
24. PRIME CONTRACTOR ORDERING FROM <strong>FEDERAL</strong> <strong>SUPPLY</strong> SCHEDULES.<br />
Prime Contractors (on cost reimbursement contracts) placing orders under <strong>Federal</strong> Supply Schedules, on<br />
behalf of a <strong>Federal</strong> Agency, shall follow the terms of the applicable schedule and authorization and include<br />
with each order –<br />
(a) A copy of the authorization from the Agency with whom the contractor has the prime<br />
contract (unless a copy was previously furnished to the <strong>Federal</strong> Supply Schedule contractor); and<br />
(b) The following statement:<br />
This order is placed under written authorization from _______ dated _______. In the<br />
event of any inconsistency between the terms and conditions of this order and those of<br />
your <strong>Federal</strong> Supply Schedule contract, the latter will govern.
TERMS AND CONDITIONS APPLICABLE TO<br />
PERPETUAL SOFTWARE LICENSES (SPECIAL ITEM NUMBER 132-33) AND<br />
MAINTENANCE (SPECIAL ITEM NUMBER 132-34) OF GENERAL PURPOSE<br />
COMMERCIAL INFORMATION TECHNOLOGY SOFTWARE<br />
1. INSPECTION/ACCEPTANCE<br />
The Contractor shall only tender for acceptance those items that conform to the requirements of this<br />
contract. The Government reserves the right to inspect or test any software that has been tendered for<br />
acceptance. The Government may require repair or replacement of nonconforming software at no increase<br />
in contract price. The Government must exercise its post-acceptance rights (1) within a reasonable time<br />
after the defect was discovered or should have been discovered; and (2) before any substantial change<br />
occurs in the condition of the software, unless the change is due to the defect in the software.<br />
2. GUARANTEE/WARRANTY<br />
a. Unless specified otherwise in this contract, the Contractor’s standard commercial<br />
guarantee/warranty as stated in the contract’s commercial pricelist will apply to this contract.<br />
b. The Contractor does not warrant or imply merchantability or fitness for use for particular purpose.<br />
c. Limitation of Liability. Except as otherwise provided by an express or implied warranty, the<br />
Contractor will not be liable to the Government for consequential damages resulting from any defect or<br />
deficiencies in accepted items.<br />
3. TECHNICAL <strong>SERVICE</strong>S<br />
The Contractor, without additional charge to the Government, shall provide a hot line technical support<br />
number 1-800-334-1553 for the purpose of providing user assistance and guidance in the implementation of<br />
the software. The technical support number is available from 8:00 a.m. to 5:00 p.m., Monday through<br />
Friday. Eastern Time.<br />
4. SOFTWARE MAINTENANCE<br />
a. Software maintenance service shall include the following:<br />
NetFacade software maintenance includes Help Desk Hotline assistance via phone, Monday through<br />
Friday, 8:00 a.m. 5:00 p.m., and via email 24/7. This begins from the moment of installation through the<br />
length of the one year service agreement. A trouble ticket procedure is in place to report any problems<br />
which ensures all issues are addressed and closed out in a timely manner. Help Desk will support matters<br />
relating to both the operation and configuration of NetFacade in order to maximize its effectiveness.<br />
NetFacade technicians will assist in understanding log reporting features and analysis. A web site is<br />
available for support documents as well as to report problems/issues.<br />
b. Invoices for maintenance service shall be submitted by the Contractor on a quarterly or monthly<br />
basis, after the completion of such period. Maintenance charges must be paid in arrears (31 U.S.C. 3324).<br />
PROMPT PAYMENT DISCOUNT, IF APPLICABLE, SHALL BE SHOWN ON THE INVOICE. The<br />
NetFacade Software Maintenance, as described herein, is available at $5,385 per year, after the first<br />
year. The initial one year of maintenance is included in the price of the software license.
c. The Contractor agrees to provide updates and maintenance service for the software after a<br />
perpetual license has accrued, at the prices and terms of Special Item Number l32-34, if the licensee elects<br />
to order such services. Title to the software shall remain with the Contractor.<br />
5. UTILIZATION LIMITATIONS - (132-32, 132-33, AND 132-34)<br />
a. Software acquisition is limited to commercial computer software defined in FAR Part 2.101.<br />
b. When acquired by the Government, commercial computer software and related documentation so<br />
legend shall be subject to the following:<br />
(1) Title to and ownership of the software and documentation shall remain with the<br />
Contractor, unless otherwise specified.<br />
(2) Software licenses are by site and by agency. An agency is defined as a cabinet level or<br />
independent agency. The software may be used by any subdivision of the agency (service, bureau,<br />
division, command, etc.) that has access to the site the software is placed at, even if the<br />
subdivision did not participate in the acquisition of the software. Further, the software may be<br />
used on a sharing basis where multiple agencies have joint projects that can be satisfied by the use<br />
of the software placed at one agency's site. This would allow other agencies access to one<br />
agency's database. For Government public domain databases, user agencies and third parties may<br />
use the computer program to enter, retrieve, analyze and present data. The user agency will take<br />
appropriate action by instruction, agreement, or otherwise, to protect the Contractor's proprietary<br />
property with any third parties that are permitted access to the computer programs and<br />
documentation in connection with the user agency's permitted use of the computer programs and<br />
documentation. For purposes of this section, all such permitted third parties shall be deemed<br />
agents of the user agency.<br />
(3) Except as is provided in paragraph 8.b(2) above, the Government shall not provide or<br />
otherwise make available the software or documentation, or any portion thereof, in any form, to<br />
any third party without the prior written approval of the Contractor. Third parties do not include<br />
prime Contractors, subcontractors and agents of the government who have the Government's<br />
permission to use the licensed software and documentation at the facility, and who have agreed to<br />
use the licensed software and documentation only in accordance with these restrictions. This<br />
provision does not limit the right of the Government to use software, documentation, or<br />
information therein, which the Government may already have or obtains without restrictions.<br />
(4) The Government shall have the right to use the computer software and documentation<br />
with the computer for which it is acquired at any other facility to which that computer may be<br />
transferred, or in cases of disaster recovery, the Government has the right to transfer the software<br />
to another site if the Government site for which it is acquired is deemed to be unsafe for<br />
Government personnel; to use the computer software and documentation with a backup computer<br />
when the primary computer is inoperative; to copy computer programs for safekeeping (archives)<br />
or backup purposes; to transfer a copy of the software to another site for purposes of<br />
benchmarking new hardware and/or software; and to modify the software and documentation or<br />
combine it with other software, provided that the unmodified portions shall remain subject to these<br />
restrictions.<br />
(5) "Commercial Computer Software" may be marked with the Contractor's standard<br />
commercial restricted rights legend, but the schedule contract and schedule pricelist, including this<br />
clause, "Utilization Limitations" are the only governing terms and conditions, and shall take<br />
precedence and supersede any different or additional terms and conditions included in the standard<br />
commercial legend.
6. SOFTWARE CONVERSIONS - (132-32 AND 132-33)<br />
Full monetary credit will be allowed to the Government when conversion from one version of the software<br />
to another is made as the result of a change in operating system, or from one computer system to another.<br />
Under a perpetual license (132-33), the purchase price of the new software shall be reduced by the amount<br />
that was paid to purchase the earlier version.<br />
7. DESCRIPTIONS AND EQUIPMENT COMPATIBILITY<br />
NETFACADE SOFTWARE PRODUCT DESCRIPTION AND PRICING<br />
NetFacade Intrusion Detection technology provides a new alerting capability for use by network security<br />
or management personnel of an unauthorized intrusion onto your network. NetFacade adds an additional<br />
perimeter of monitoring for intrusions, it complements Firewalls and Intrusion Detection <strong>Systems</strong> and<br />
reduces the possibility of intrusions occurring without alerting to the activity. In addition, it has a secondary<br />
effect of distracting intruders from probing and attacking the real hosts on the network. NetFacade <br />
simulates network hosts running seemingly vulnerable services. A scan of the range of IP addresses<br />
NetFacade is simulating will return information on the simulated services as if they were real network<br />
services running on actual hosts. Since there are no actual users of these virtual network simulated hosts,<br />
all traffic to them is considered to be suspicious. All traffic to NetFacade is logged and then an alert of<br />
the activity that is occurring on the simulated hosts is sent to the security administrator/management<br />
personnel. These alerts can be configured at various levels and with specific response actions. Because of<br />
this capability NetFacade can identify all new and unknown attacks which can be tagged as new<br />
signatures for your Intrusion Detection <strong>Systems</strong> and Firewalls.<br />
NetFacade Version 1.3 now available includes:<br />
Intrusion Detection Features:<br />
Elimination of network bandwidth limitations since NetFacade has to be concerned only with the traffic<br />
going to its simulated hosts<br />
A high level of data reduction and low rate of false-positive type incidents since the all traffic to<br />
NetFacade is suspicious<br />
No limit on the number and types of attacks that are detected, including new and unknown types attacks<br />
Distraction of attackers away from the real hosts that NetFacade is protecting<br />
IP Filtering used to only allow access from specified administration workstations<br />
<strong>Network</strong> Simulation Features:<br />
Simulation of up to a Class C IP network of virtual hosts<br />
Simulates an entire Class C network or any subnet therein<br />
<strong>Network</strong> address space can be dedicated or an existing network can be used to "interleave" simulated hosts<br />
with actual hosts<br />
Appropriate responses to operating system fingerprint IP packets<br />
Host Simulation Features:<br />
Simulation of eight different operating systems:<br />
IOS 11.1(4) for Cisco Routers<br />
IRIX 1.0 for x86<br />
Redhat Linux 5.0 for x86<br />
Redhat Linux 5.1 for x86<br />
Solaris 2.5.1 for Sun Sparc<br />
Solaris 2.6 for Sun Sparc<br />
SunOS 4.1.4 for Sun Sparc<br />
Microsoft NT 4.0 for x86
Simulation of thirteen different services with versions appropriate for the different operating systems,<br />
including:<br />
FTP (wu-2.4.2-academ[BETA-12](1), System V Release 4.0, and SunOS4.1 versions)<br />
Telnet (appropriate versions for each operating system)<br />
SSH (SSH Communications Security Ltd's 1.2.26 and 2.0.9 versions)<br />
SMTP (SMI-4.1, ESMTP 8.8.7, ESMTP 8.9.1 and generic versions)<br />
HTTP (Apache 1.2.6, Netscape Enterprise 3.0, and Microsoft IIS 4.0 versions)<br />
IMAP (IMAP4rev1 v10.205, v10.223, v10.234 and v9.0(157) versions)<br />
Echo (UDP and TCP versions)<br />
Daytime (UDP and TCP versions)<br />
Finger<br />
Rlogin<br />
Portmap/tcpbind (UDP and TCP versions)<br />
Mountd (UDP and TCP versions)<br />
Rusers (UDP version)<br />
NFS<br />
Configuration/Monitoring Features:<br />
Configuration and monitoring performed through web-based interface<br />
Connections only allowed from specified workstations<br />
Session encrypted using SSL<br />
Connection authenticated using a username and password<br />
Friendly and flexible configuration of network, hosts, and simulated user accounts<br />
User-friendly configuration of alert recipients<br />
Interface for viewing logs<br />
Status report generation capability<br />
Logging Features:<br />
All activity to NetFacade is logged<br />
All logs record the source IP address<br />
Used to determine what the potential threat is to the rest of the system<br />
Activity is logged two ways<br />
All TCP/IP packets received or sent by the system are logged<br />
All service façades log the data they receive in hexadecimal and ASCII format for ease of determining the<br />
type of attack<br />
Activity logs stored in an a SQL database<br />
Web-based interface to activity reports<br />
Reporting based on user-defined parameters<br />
Alerting Features:<br />
Alerts accomplished via e-mail notification to configured list of recipients<br />
Recipients alerted periodically if any activity has been detected<br />
Frequency of alerts is configurable<br />
Alert includes a summary of the activity including the source IP addresses, the targeted service/port and the<br />
amount of traffic received<br />
Enhanced responsiveness to port sweeps<br />
Flexibility in attack recognition and forensics<br />
Automated attack recognition<br />
Multiple alerting methods<br />
Multiple alert levels<br />
Web-based configuration of alert levels and associated actions<br />
Web-based configuration of associating alert levels with specific types of activity<br />
Automated attack recognition tied to alerting<br />
Unknown attacks are identified and can be used as new attack signatures for IDSs and FWs<br />
Alerting based on the type of attack and the alert level configured for that type of attack
Hardware And Software Operating System Requirements:<br />
The NetFacade software is designed for a Sun Microsystems Ultra 5 running Sun Solaris 7.<br />
The recommended minimum configuration is as follows:<br />
333MHz<br />
128 MB RAM<br />
9 GB Hard Drive<br />
32 x CD-ROM<br />
To ensure the security of the NetFacade system, the Solaris 7 patches recommended by Sun should be<br />
installed. Please refer to the Solaris documentation for instructions on how to install the operating system<br />
and patches. Refer to the SunSolve Online Patch Access web site (sunsolve.sun.com/pubcgi/pubpatchpage.pl)<br />
for the latest list of available and recommended patches for Solaris 7.<br />
When installing the operating system, the file systems should be configured as follows to ensure the correct<br />
amount of disk space for NetFacade:<br />
File System Recommended Size<br />
/ 512 MB<br />
/usr<br />
default<br />
swap<br />
256 MB (2x memory size)<br />
overlap default<br />
/export/home remaining blocks<br />
NetFacade is a trademark of <strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong>, a <strong>Verizon</strong> Company, under license. All<br />
other marks are the properties of their respective owners.<br />
Pricing:<br />
1. NetFacade software version 1.3 - Virtual Intrusion Detection Technology (software), User's Guide,<br />
automatic version upgrades (initial year), help desk (initial year), training and remote<br />
installation/configuration support (initial year).<br />
$14,255<br />
8. RIGHT-TO-COPY PRICING<br />
The offer is for perpetual license software only: right-to-copy licensing is not offered.
TERMS AND CONDITIONS APPLICABLE TO INFORMATION<br />
TECHNOLOGY (IT)<br />
PROFESSIONAL <strong>SERVICE</strong>S (SPECIAL ITEM NUMBER 132-51)<br />
1. SCOPE<br />
a. The prices, terms and conditions stated under Special Item Number 132-51 Information<br />
Technology Professional Services and Special Item Number 132-52 Electronic Commerce Services apply<br />
exclusively to IT/EC Services within the scope of this Information Technology Schedule.<br />
b. The Contractor shall provide services at the Contractor’s facility and/or at the Government<br />
location, as agreed to by the Contractor and the ordering office.<br />
2. PERFORMANCE INCENTIVES<br />
a. When using a performance based statement of work, performance incentives may be agreed upon<br />
between the Contractor and the ordering office on individual fixed price orders or Blanket Purchase<br />
Agreements, for fixed price tasks, under this contract in accordance with this clause.<br />
b. The ordering office must establish a maximum performance incentive price for these services<br />
and/or total solutions on individual orders or Blanket Purchase Agreements.<br />
c. To the maximum extent practicable, ordering offices shall consider establishing incentives where<br />
performance is critical to the agency’s mission and incentives are likely to motivate the contractor.<br />
Incentives shall be based on objectively measurable tasks.<br />
d. The above procedures do not apply to Time and Material or labor hour orders.<br />
3. ORDERING PROCEDURES FOR <strong>SERVICE</strong>S (REQUIRING A STATEMENT OF WORK<br />
FAR 8.402 contemplates that GSA may occasionally find it necessary to establish special ordering<br />
procedures for individual <strong>Federal</strong> Supply Schedules or for some Special Item Numbers (SINs) within a<br />
Schedule. GSA has established special ordering procedures for services that require a Statement of Work.<br />
These special ordering procedures take precedence over the procedures in FAR 8.404 (b)(2) through (b)(3).<br />
GSA has determined that the prices for services contained in the contractor’s price list applicable to this<br />
Schedule are fair and reasonable. However, the ordering office using this contract is responsible for<br />
considering the level of effort and mix of labor proposed to perform a specific task being ordered and for<br />
making a determination that the total firm-fixed price or ceiling price is fair and reasonable.<br />
(a) When ordering services, ordering offices shall —<br />
(1) Prepare a Request (Request for Quote or other communication tool):<br />
(i) A statement of work (a performance-based statement of work is preferred) that<br />
outlines, at a minimum, the work to be performed, location of work, period of<br />
performance, deliverable schedule, applicable standards, acceptance criteria, and any<br />
special requirements (e.g., security clearances, travel, special knowledge, etc.) should be<br />
prepared.<br />
(ii) The request should include the statement of work and request the contractors to<br />
submit either a firm-fixed price or a ceiling price to provide the services outlined in the<br />
statement of work. A firm-fixed price order shall be requested, unless the ordering office<br />
makes a determination that it is not possible at the time of placing the order to estimate<br />
accurately the extent or duration of the work or to anticipate cost with any reasonable
degree of confidence. When such a determination is made, a labor hour or time-andmaterials<br />
proposal may be requested. The firm-fixed price shall be based on the rates in<br />
the schedule contract and shall consider the mix of labor categories and level of effort<br />
required to perform the services described in the statement of work. The firm-fixed price<br />
of the order should also include any travel costs or other incidental costs related to<br />
performance of the services ordered, unless the order provides for reimbursement of<br />
travel costs at the rates provided in the <strong>Federal</strong> Travel or Joint Travel Regulations. A<br />
ceiling price must be established for labor-hour and time-and-materials orders.<br />
(iii) The request may ask the contractors, if necessary or appropriate, to submit a<br />
project plan for performing the task, and information on the contractor’s experience<br />
and/or past performance performing similar tasks.<br />
(iv) The request shall notify the contractors what basis will be used for selecting the<br />
contractor to receive the order. The notice shall include the basis for determining whether<br />
the contractors are technically qualified and provide an explanation regarding the<br />
intended use of any experience and/or past performance information in determining<br />
technical qualification of responses. If consideration will be limited to schedule<br />
contractors who are small business concerns as permitted by paragraph (2)(i) below, the<br />
request shall notify the contractors that will be the case.<br />
(2) Transmit the Request to Contractors:<br />
(i) Based upon an initial evaluation of catalogs and price lists, the ordering office<br />
should identify the contractors that appear to offer the best value (considering the scope<br />
of services offered, pricing and other factors such as contractors’ locations, as<br />
appropriate). When buying IT professional services under SIN 132—51 ONLY, the<br />
ordering office, at its discretion, may limit consideration to those schedule contractors<br />
that are small business concerns. This limitation is not applicable when buying supplies<br />
and/or services under other SINs as well as SIN 132-51. The limitation may only be used<br />
when at least three (3) small businesses that appear to offer services that will meet the<br />
agency’s needs are available, if the order is estimated to exceed the micro-purchase<br />
threshold.<br />
(ii) The request should be provided to three (3) contractors if the proposed order is<br />
estimated to exceed the micro-purchase threshold, but not exceed the maximum order<br />
threshold. For proposed orders exceeding the maximum order threshold, the request<br />
should be provided to additional contractors that offer services that will meet the<br />
agency’s needs. Ordering offices should strive to minimize the contractors’ costs<br />
associated with responding to requests for quotes for specific orders. Requests should be<br />
tailored to the minimum level necessary for adequate evaluation and selection for order<br />
placement. Oral presentations should be considered, when possible.<br />
(3) Evaluate Responses and Select the Contractor to Receive the Order:<br />
After responses have been evaluated against the factors identified in the request, the order should<br />
be placed with the schedule contractor that represents the best value. (See FAR 8.404.)<br />
(b) The establishment of <strong>Federal</strong> Supply Schedule Blanket Purchase Agreements (BPAs) for<br />
recurring services is permitted when the procedures outlined herein are followed. All BPAs for<br />
services must define the services that may be ordered under the BPA, along with delivery or<br />
performance time frames, billing procedures, etc. The potential volume of orders under BPAs,<br />
regardless of the size of individual orders, may offer the ordering office the opportunity to secure<br />
volume discounts. When establishing BPAs, ordering offices shall —<br />
(1) Inform contractors in the request (based on the agency’s requirement) if a single BPA or<br />
multiple BPAs will be established, and indicate the basis that will be used for selecting the<br />
contractors to be awarded the BPAs.<br />
(i) SINGLE BPA: Generally, a single BPA should be established when the ordering<br />
office can define the tasks to be ordered under the BPA and establish a firm-fixed price or
ceiling price for individual tasks or services to be ordered. When this occurs, authorized<br />
users may place the order directly under the established BPA when the need for service<br />
arises. The schedule contractor that represents the best value should be awarded the BPA.<br />
(See FAR 8.404.)<br />
(ii) MULTIPLE BPAs: When the ordering office determines multiple BPAs are<br />
needed to meet its requirements, the ordering office should determine which contractors<br />
can meet any technical qualifications before establishing the BPAs. When multiple<br />
BPAs are established, the authorized users must follow the procedures in (a)(2)(ii) above<br />
and then place the order with the Schedule contractor that represents the best value.<br />
(2) Review BPAs Periodically: Such reviews shall be conducted at least annually. The<br />
purpose of the review is to determine whether the BPA still represents the best value. (See FAR<br />
8.404.)<br />
(c) The ordering office should give preference to small business concerns when two or more<br />
contractors can provide the services at the same firm-fixed price or ceiling price.<br />
(d) When the ordering office’s requirement involves both products as well as executive,<br />
administrative and/or professional, services, the ordering office should total the prices for the products and<br />
the firm-fixed price for the services and select the contractor that represents the best value. (See FAR<br />
8.404.)<br />
The ordering office, at a minimum, should document orders by identifying the contractor from which the<br />
services were purchased, the services purchased, and the amount paid. If other than a firm-fixed price<br />
order is placed, such documentation should include the basis for the determination to use a labor-hour or<br />
time-and-materials order. For agency requirements in excess of the micro-purchase threshold, the order file<br />
should document the evaluation of Schedule contractors’ quotes that formed the basis for the selection of<br />
the contractor that received the order and the rationale for any trade-offs made in making the selection.<br />
Ordering procedures for other services available on schedule at fixed prices for specifically defined<br />
services or tasks should use the procedures in FAR 8.404. These procedures are listed in the pricelist,<br />
under “Information for Ordering Offices,” paragraph #12.<br />
4. ORDER<br />
a. Agencies may use written orders, EDI orders, blanket purchase agreements, individual purchase<br />
orders, or task orders for ordering services under this contract. Blanket Purchase Agreements shall not<br />
extend beyond the end of the contract period; all services and delivery shall be made and the contract terms<br />
and conditions shall continue in effect until the completion of the order. Orders for tasks which extend<br />
beyond the fiscal year for which funds are available shall include FAR 52.232-19 Availability of Funds for<br />
the Next Fiscal Year. The purchase order shall specify the availability of funds and the period for which<br />
funds are available.<br />
b. All task orders are subject to the terms and conditions of the contract. In the event of conflict<br />
between a task order and the contract, the contract will take precedence.<br />
5. PERFORMANCE OF <strong>SERVICE</strong>S<br />
a. The Contractor shall commence performance of services on the date agreed to by the Contractor<br />
and the ordering office.<br />
b. The Contractor agrees to render services only during normal working hours, unless otherwise<br />
agreed to by the Contractor and the ordering office.<br />
c. The Agency should include the criteria for satisfactory completion for each task in the Statement<br />
of Work or Delivery Order. Services shall be completed in a good and workmanlike manner.
d. Any Contractor travel required in the performance of IT/EC Services must comply with the<br />
<strong>Federal</strong> Travel Regulation or Joint Travel Regulations, as applicable, in effect on the date(s) the travel is<br />
performed. Established <strong>Federal</strong> Government per diem rates will apply to all Contractor travel. Contractors<br />
cannot use GSA city pair contracts.<br />
6. INSPECTION OF <strong>SERVICE</strong>S<br />
The Inspection of Services–Fixed Price (AUG 1996) clause at FAR 52.246-4 applies to firm-fixed price<br />
orders placed under this contract. The Inspection–Time-and-Materials and Labor-Hour (JAN 1986) clause<br />
at FAR 52.246-6 applies to time-and-materials and labor-hour orders placed under this contract.<br />
7. RESPONSIBILITIES OF THE CONTRACTOR<br />
The Contractor shall comply with all laws, ordinances, and regulations (<strong>Federal</strong>, State, City, or otherwise)<br />
covering work of this character. If the end product of a task order is software, then FAR 52.227-14 Rights<br />
in Data – General, may apply.<br />
8. RESPONSIBILITIES OF THE GOVERNMENT<br />
Subject to security regulations, the ordering office shall permit Contractor access to all facilities necessary<br />
to perform the requisite IT/EC Services.<br />
9. INDEPENDENT CONTRACTOR<br />
All IT/EC Services performed by the Contractor under the terms of this contract shall be as an independent<br />
Contractor, and not as an agent or employee of the Government.<br />
10. ORGANIZATIONAL CONFLICTS OF INTEREST<br />
a. Definitions.<br />
“Contractor” means the person, firm, unincorporated association, joint venture, partnership, or corporation<br />
that is a party to this contract.<br />
“Contractor and its affiliates” and “Contractor or its affiliates” refers to the Contractor, its chief executives,<br />
directors, officers, subsidiaries, affiliates, subcontractors at any tier, and consultants and any joint venture<br />
involving the Contractor, any entity into or with which the Contractor subsequently merges or affiliates, or<br />
any other successor or assignee of the Contractor.<br />
An “Organizational conflict of interest” exists when the nature of the work to be performed under a<br />
proposed Government contract, without some restriction on activities by the Contractor and its affiliates,<br />
may either (i) result in an unfair competitive advantage to the Contractor or its affiliates or (ii) impair the<br />
Contractor’s or its affiliates’ objectivity in performing contract work.<br />
b. To avoid an organizational or financial conflict of interest and to avoid prejudicing the best<br />
interests of the Government, ordering offices may place restrictions on the Contractors, its affiliates, chief<br />
executives, directors, subsidiaries and subcontractors at any tier when placing orders against schedule<br />
contracts. Such restrictions shall be consistent with FAR 9.505 and shall be designed to avoid, neutralize,<br />
or mitigate organizational conflicts of interest that might otherwise exist in situations related to individual<br />
orders placed against the schedule contract. Examples of situations, which may require restrictions, are<br />
provided at FAR 9.508.
11 INVOICES<br />
The Contractor, upon completion of the work ordered, shall submit invoices for IT/EC services. Progress<br />
payments may be authorized by the ordering office on individual orders if appropriate. Progress payments<br />
shall be based upon completion of defined milestones or interim products. Invoices shall be submitted<br />
monthly for recurring services performed during the preceding month.<br />
12. PAYMENTS<br />
For firm-fixed price orders the Government shall pay the Contractor, upon submission of proper invoices or<br />
vouchers, the prices stipulated in this contract for service rendered and accepted. Progress payments shall<br />
be made only when authorized by the order. For time-and-materials orders, the Payments under<br />
Time-and-Materials and Labor-Hour Contracts (Alternate I (APR 1984)) at FAR 52.232-7 applies to<br />
time-and-materials orders placed under this contract. For labor-hour orders, the Payment under<br />
Time-and-Materials and Labor-Hour Contracts (FEB 2002) (Alternate II (FEB 2002)) at FAR 52.232-7<br />
applies to labor-hour orders placed under this contract.<br />
13. RESUMES<br />
Resumes shall be provided to the GSA Contracting Officer or the user agency upon request.<br />
14. INCIDENTAL SUPPORT COSTS<br />
Incidental support costs are available outside the scope of this contract. The costs will be negotiated<br />
separately with the ordering agency in accordance with the guidelines set forth in the FAR.<br />
15. APPROVAL OF SUBCONTRACTS<br />
The ordering activity may require that the Contractor receive, from the ordering activity's Contracting<br />
Officer, written consent before placing any subcontract for furnishing any of the work called for in a task<br />
order.<br />
16. DESCRIPTION OF IT/EC <strong>SERVICE</strong>S AND PRICING<br />
VERIZON <strong>SERVICE</strong> DESCRIPTIONS<br />
<strong>Verizon</strong> <strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong><br />
<strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong> (FNS), a wholly-owned company of <strong>Verizon</strong> Technology Corporation,<br />
designs, implements, operates, and maintains mission-critical, wide-area networks for <strong>Federal</strong> and<br />
commercial clients. Members of FNS work with the <strong>Verizon</strong> Technology Organization to integrate secure,<br />
reliable data services, such as DSL, VPNs, and a host of other access, security, Web, and advanced<br />
networking products and services. Our staff works in customer locations around the world, and we have<br />
several office locations in the metropolitan Washington DC area.<br />
FNS focuses on several key business areas:<br />
<strong>Network</strong> Services. FNS designs and implements the full range of access methods to suit different<br />
performance and security needs. A team of network professionals helps clients develop <strong>Network</strong><br />
Operations Center (NOC) requirements, network analysis, engineering, and designs. This includes NOC<br />
performance analyses, such as throughput, choke points, metric monitoring, and modeling. The team's<br />
network expertise spans local area networks through metropolitan area and wide area networks.<br />
<strong>Network</strong> Security Services. Our consulting services give clients the benefit of the experience of a<br />
seasoned team of widely recognized experts in networking technologies. FNS network consulting services<br />
include the following:
- Penetration Analysis Ethical Hacking<br />
- Security Assessment<br />
- Security Design<br />
- Security Implementation<br />
- Security Policies and Procedures<br />
- Internet Security<br />
- Managed Security Products and Services<br />
- Virtual Private <strong>Network</strong>s.<br />
Engineering Services. FNS program managers routinely handle complex programs requiring staffing,<br />
execution, monitoring, reporting, and re-engineering customers' processes to ensure that IT network designs<br />
meet current and future goals and objectives. At customer facilities, FNS professionals provide site design,<br />
configuration management, preparation, and installation of internetworking solutions that will meet<br />
customer needs in the new millennium. FNS also offers a suite of back-office services that include network<br />
management, invoicing, billing, and operations support.<br />
Support Services. The people who best understand networking provide our substantial support services.<br />
We can identify potential issues before they develop, guiding customers' staff through maintenance and<br />
operations, and troubleshooting problems quickly and efficiently. FNS offers a comprehensive suite of<br />
support services, including the following:<br />
- Hardware Maintenance and Instruction Support<br />
- <strong>Network</strong> Modeling and Performance Assessment<br />
- End-User Help Desk and Customer Support<br />
Today, FNS provides network support in the areas of operations, maintenance, engineering, and program<br />
management for DISA’s IP router networks, ATM networks, GCCS networks, the Treasury<br />
Communications System, and other mission-critical Government and commercial networks. Our customers<br />
have been highly satisfied with our contract performance, as evidenced by the longevity of continual<br />
support (since 1985 with Treasury, since 1982 with DISA, and before that with DARPA), and high praise<br />
from our customers (including numerous letters of commendation to both the corporation and individual<br />
employees). Additionally, DISA, the DARPA JPO, Treasury, and other customers have recognized our<br />
company for its efforts in inserting leading-edge technology into networks, and successfully integrating this<br />
technology with legacy systems and network components.<br />
Information Management. FNS develops and implements advanced database and information systems to<br />
support distributed applications over secure networks. Our extensive experience in all the technologies<br />
integral to effective database and information management includes:<br />
- Database design and implementation<br />
- Software architecture and development<br />
- <strong>Systems</strong> implementation and integration<br />
- Inter/intranetworking<br />
- <strong>Network</strong>ing security<br />
Information Security. FNS conducts research and development on high-value or difficult information<br />
security problems. We solve complex security problems not yet addressed by the commercial sector. Our<br />
research and development efforts encompass many significant security programs and critical research areas,<br />
such as Information Assurance, Protocol Design, and Security Policy Specification and Management.<br />
<strong>Network</strong>ing. FNS leading-edge research advances the state of the Internet; our practical solutions enhance<br />
the reliability of wide area networks; and our advanced technologies enable information distribution,<br />
mobile tactical networking, and communications connectivity network management.<br />
<strong>Verizon</strong> is dedicated to the task of bringing our extensive portfolio of Information Technology products and<br />
services to the United States Government. <strong>Verizon</strong> is particularly interested in supporting our DOD and<br />
Home Security Agencies. It is our desire to win the confidence of the United States Air Force through<br />
consistent excellent performance and client satisfaction. We thank you for taking the time to consider our<br />
statement of interest. We look forward to meeting with the Air Force Pentagon Communications Agency<br />
to provide more information about our new <strong>Verizon</strong>.<br />
<strong>Verizon</strong> Data Center Installation. <strong>Verizon</strong> uses a staged migration approach by data center and by<br />
platform. With this approach, we can migrate one data center at a time and, within that data center, we<br />
migrate the mainframe environment first, then the midrange, and finally the other servers. For certain small<br />
servers, such as NT servers, we advise working with the customer during due diligence to determine the<br />
best approach for the customer’s location and operational management.
To facilitate the migration, <strong>Verizon</strong> can purchase or lease swing equipment. This allows the initial<br />
migration of processing, so that the customer’s existing equipment can be relocated to the <strong>Verizon</strong> IT<br />
environment. After all migrations are complete, we can dispose of the swing equipment or use it as a<br />
replacement for existing equipment. <strong>Network</strong> monitoring would be migrated during the initial moves.<br />
<strong>Verizon</strong> understands the personal impact to individual employees affected by an outsourcing transition.<br />
We also understand how important knowledge retention is with a transition. We make every effort to<br />
ensure that customer employees involved in this process are treated honestly and fairly, and that critical<br />
operational knowledge is not lost in the transition and migration process. As the migration of each data<br />
center is completed, <strong>Verizon</strong> may offer certain key employees positions with <strong>Verizon</strong>.<br />
<strong>Verizon</strong> Data Center Operations. Data center operations encompass the services associated with the<br />
execution of customer test and production online and batch applications. Data center operations occur 24<br />
hours a day, 7 days a week, and provide the services needed to ensure customer applications are available<br />
and functioning as business needs dictate.<br />
Operations support includes the ongoing maintenance and monitoring activities required to ensure that the<br />
data center operation runs smoothly and efficiently. <strong>Verizon</strong> recognizes that preventive maintenance is an<br />
important and necessary part of a successful data center processing operation. We adhere to monitoring<br />
and maintenance procedures that keep all hardware operating at peak performance levels and efficiencies.<br />
Our maintenance procedures can be tailored for each device type and their respective maintenance<br />
requirements. Regularly scheduled maintenance avoids disruption to the customer’s business processing<br />
requirements. Additionally, regular reports are produced through maintenance procedures and processes<br />
that reflect the potential for, or actual development of, problem areas.<br />
<strong>Verizon</strong> operators are onsite 24 hours a day to proactively monitor system performance and to diagnose and<br />
resolve any problems that might occur. Issues, concerns, or problems with the customer’s processing<br />
environment are logged as they occur. Established procedures are used to diagnose and resolve the<br />
problem, or to dispatch the problem to the appropriate support organization. Our responsibility is to ensure<br />
that there is no disruption to the customer’s production environment.<br />
<strong>Verizon</strong> IT uses SunSPARC stations to monitor and control customer system activities. These multitasking<br />
workstations allow us to monitor numerous systems and enable our operators to carry out and control tasks<br />
simultaneously. <strong>Verizon</strong> IT maintains system integrity by automating such functions as:<br />
- Console message traffic<br />
- Started task management (start, stop, and ABEND notification)<br />
- Online system performance<br />
- Online system management<br />
- Batch processing resource connection management (start, stop, and failure notification)<br />
- Batch processing automation (dataset triggers and schedule manipulation)<br />
- Exception message trapping and global notification<br />
- Message trapping and reformatting for specific purposes<br />
<strong>Verizon</strong> has used various automation tools for more than 30 years, enabling an efficient data center<br />
operation that benefits the customer.<br />
<strong>Verizon</strong> Maintenance. Preventive maintenance is vital to a successful data processing operation. <strong>Verizon</strong><br />
IT establishes and adheres to monitoring and maintenance procedures that keep all hardware operating at<br />
peak performance levels and efficiencies. The maintenance procedures employed depend on the device,<br />
maintenance requirements, outage schedules, and information reflected in reports that demonstrate the<br />
potential for, or actual development of, problem areas.<br />
If a problem is identified, the maintenance procedures and schedules take into account the risks and<br />
potential disruption to the customer’s operating environment, before determining the best course of<br />
corrective action. These activities ensure that customer hardware and system software continue running<br />
smoothly.<br />
<strong>Verizon</strong> Managed <strong>Network</strong> Solutions (MNS). Managed <strong>Network</strong> Solutions is a family of services that<br />
allow customers to let <strong>Verizon</strong> manage their increasingly complex voice and data networks. We can help
educe costs and improve network performance by offering a spectrum of services, ranging from CPE<br />
maintenance, up through end-to-end management of customers’ networks via MNS.<br />
• MNS FrameWatch. A comprehensive service that includes <strong>Verizon</strong>-provided CPE, configuration,<br />
installation, ongoing maintenance, troubleshooting, monitoring, and service-level reporting for Frame<br />
Relay <strong>Network</strong>s. <strong>Verizon</strong> provides WAN Management and Router Management.<br />
• MNS IPT Watch (IP Telephony Watch). <strong>Verizon</strong>’s MNS IPT Watch is a comprehensive<br />
management solution for the IP Telephony portion of customers’ converged Cisco networks. IPT<br />
Watch offers three levels of service–Call Manager/Server Management, IP QoS Fault Monitoring, and<br />
IP QoS Performance Monitoring–to meet customers’ specific needs. When bundled with other MNS<br />
services like <strong>Verizon</strong> Data Maintenance and SiteWatch, <strong>Verizon</strong> can offer a full out-tasked solution,<br />
unmatched in the industry, that differentiates us from all the other Cisco equipment resellers.<br />
• MNS SiteWatch (management and maintenance). <strong>Verizon</strong>'s MNS SiteWatch is a complete<br />
management and maintenance solution for customers’ data networks. SiteWatch offers three service<br />
options that give customers the flexibility to meet their specific business needs: Fault Management,<br />
Performance Management, and Configuration Management.<br />
• <strong>Verizon</strong> Data Maintenance. A comprehensive offering of support programs, premier in the industry.<br />
Data Maintenance provides maintenance and troubleshooting for customers' crucial data networks, and<br />
offers everything from telephone troubleshooting to online fault monitoring and onsite parts and labor,<br />
depending on which service option they choose:<br />
- Next Business Day (NBD) Remote<br />
- 4-Hour Remote<br />
- 8-Hour Onsite<br />
- 4-Hour Onsite<br />
- Connectivity Assurance Service<br />
• File/Print Services. <strong>Verizon</strong> supports its customer’s file/print requirements by maintaining and<br />
coordinating all file and print activities, including printed reports, and design and development of laser<br />
print forms. Services include:<br />
- Support and maintain all print hardware<br />
- Operate and manage print queues and devices<br />
- Prepare reports and distribute on schedule<br />
- Monitor and maintain consumables<br />
- Ensure all files are available during prime time<br />
- Perform activities to ensure data integrity<br />
- Execute backup procedure and perform restore when requested<br />
- Report storage utilization statistics<br />
Please note that installation options vary depending upon location, equipment manufacturer, and type.<br />
Locations such as Texas and the tri-state area also have a local <strong>Verizon</strong> installation/maintenance<br />
organization option, as well as National-based service.<br />
• Web Services - <strong>Verizon</strong> Enterprise Advantage. <strong>Verizon</strong> Enterprise Advantage (VEA)<br />
is a comprehensive Web hosting solution set that delivers the benefits of the Internet.<br />
From simple dedicated hosting to complex, integrated managed services, <strong>Verizon</strong><br />
Enterprise Advantage solutions can help companies at each stage of their Internet<br />
experience.<br />
<strong>Verizon</strong> Enterprise Advantage consists of three service lines: Enterprise Hosting, Enterprise<br />
Performance, and Enterprise Commerce. These service lines encompass modular sets of products and<br />
services delivering high-performing Web sites and E-commerce capabilities:<br />
- Enterprise Hosting. A modular offering of products and services allows customers to select<br />
Packaged Solutions, Complex Solutions, or Custom Solutions. Packaged Solutions are our core<br />
offering of pre-engineered platforms. Complex Solutions combine the components of the<br />
Common Hosting Platform, client-specific software applications, and services, such as software<br />
support. Custom Solutions are available for non-standard configurations.
- Enterprise Performance. High-availability products for Enterprise Hosting customers who have<br />
a Web site consisting of multiple servers that require high performance and availability.<br />
Enterprise Performance and Enterprise Managed Applications product lines offer performance and<br />
commerce functionality to enhance Enterprise Hosting solutions.<br />
Enterprise Performance is a suite of performance enhancements designed to ensure server<br />
availability (minimum downtime) and server response (minimum delay). Services such as Load<br />
Balancing, Site Accelerator, Site Replication, and Traffic Distribution are available under this<br />
offering. In addition, more demanding service level agreements are offered under these services:<br />
- Load Balancing. This service is for businesses with high-traffic Web sites that require<br />
scalability and additional system performance, while minimizing downtime for missioncritical<br />
applications. This service balances the traffic load between web servers in the same<br />
data center. It automatically routes traffic to other servers if one is down.<br />
Load Balancing balances network load by directing network connections to the server with<br />
the least number of open connections. It attempts to maintain an equal number of<br />
simultaneous sessions on all servers (assuming all servers have the same capacity). A<br />
different algorithm is used for servers with large differences in capacity.<br />
- Site Accelerator-Web Caching. Caching is based on the idea that some web site content is<br />
requested frequently, while other content is seldom requested at all. It places frequently used<br />
content closer to end users by geographically distributed caching servers. A web cache is a<br />
computer system that monitors web object requests, and stores objects it retrieves from a<br />
server. On subsequent requests for the same object, the cache delivers the object from its<br />
storage, rather than passing the request on to the origin server. This approach accelerates web<br />
page downloads, reduces the number of requests to the origin server, making it more<br />
responsive and reducing bandwidth as much as 35 percent. Without caching, all traffic must<br />
travel to the origin server every time a page is requested, resulting in potentially long delays<br />
and user frustration.<br />
Since every web object changes over time, caches also determine whether or not their copy of<br />
an object is still "fresh" or whether they need to retrieve a new copy from the origin server.<br />
Web caching is particularly suited for static content, such as logos and other images and html.<br />
- Traffic Distribution/ Hopscotch. Designed for customers with high-traffic Web sites that are<br />
hosted at multiple data centers. Geographically distributed mirrored web servers provide the<br />
best end-to-end response and site redundancy. Enterprise Performance products offer a tiered<br />
approach to distributed hosting, starting out with local load balancing, moving up to caching,<br />
and finally to geographically distributed servers in multiple data centers.<br />
- Site Replication. Designed for businesses who need high availability of Web hosting, without<br />
the overhead associated with replicating files, and to ensure that content on all servers is<br />
synchronized. Distribution hosting in the same or different data centers requires the server<br />
content to be mirrored. Site Replicator is a tool for making sure that the content across all<br />
servers is the same, and that the data are synchronized. Site Replicator provides automatic<br />
content update and replication between a master Web server and multiple slave Web servers.<br />
It updates content on a scheduled, periodic, or on-demand basis.<br />
- Enterprise Commerce. A combination of pre-configured and custom applications for Enterprise<br />
Hosting customers covering a wide range of E-business solutions.<br />
• 24/7 Help desk and Applications - <strong>Verizon</strong> Managed Help Desk Services. Managed Help Desk<br />
Services provide customer end users with a single point of contact for computer technical support.<br />
The service utilizes highly trained and experienced staff to efficiently support customer end users<br />
experiencing problems with their computers. The help desk also assists end users by answering<br />
“How To Do” type questions for supported software applications.<br />
<strong>Verizon</strong> provides fast, reliable, and courteous support, meeting today’s demands for efficient computer<br />
assistance that increases end user productivity and satisfaction. Our help desks provide solutions for<br />
issues that are help desk resolvable, while educating end users in the process. The help desk is staffed<br />
to answer every call and provide technical expertise with the initial point of contact, eliminating the
need for frustrating voicemails that lead to user dissatisfaction. Our goal is to become a strategic<br />
partner with our customers in providing satisfaction to their end users.<br />
<strong>Verizon</strong> also isolates non-help desk resolvable problems, and tracks issues that need to be escalated to<br />
customer-defined contacts, such as onsite maintenance personnel. <strong>Verizon</strong> takes ownership of the<br />
problem, providing satisfaction in that the customer end user only needs to contact one entity to get<br />
assistance.<br />
Customers are provided exceptional web-based reporting for all calls received, including statistics,<br />
such as average call answer time, resolution statistics, problems categorized by applications and/or<br />
departments, call abandon rates, and a listing of repeat callers.<br />
Managed Help Desk will also receive calls, create tickets, and escalate problems for applications not<br />
directly supported. This allows the customer to have one database for all problems; calls the help desk<br />
handles and calls the help desk escalates.<br />
<strong>Verizon</strong> provides a financially cost-effective solution for our customers who choose to out-task the<br />
responsibilities of provisioning and maintaining computer help desk operations. <strong>Verizon</strong> can leverage<br />
the investment in people, processes, and systems currently in place, to run a professional help desk.<br />
We maintain a quality help desk to serve end users, so that our customers can focus on their core<br />
business. <strong>Verizon</strong> Managed Help Desk Services remove the following customer responsibilities that<br />
are associated with provisioning a help desk in-house:<br />
- Staffing agents<br />
- Providing technical training for agents<br />
- Supervising help desk agents and other help desk personnel<br />
- Scaling for growth and unexpected spikes of call volume<br />
- Provisioning and maintaining software, hardware, and work space requirements<br />
Managed Help Desk Services are performed from the <strong>Verizon</strong> Enterprise Management Center, a<br />
57,000 square foot building located in Austin TX, which operates 24 hours a day, 365 days a year.<br />
Supported Applications. <strong>Verizon</strong> provides end user help desk support for the following desktop<br />
applications:<br />
- Microsoft Operating <strong>Systems</strong><br />
- Norton Anti-Virus<br />
- Microsoft Office<br />
- Lotus Notes<br />
- Internet Explorer and Netscape Web Browser - Microsoft Outlook/Exchange<br />
Support
Security Services (Antivirus program, account management, domain management; Communications<br />
security; <strong>Network</strong> security (information assurance)<br />
<strong>Verizon</strong> Security Consulting Services. <strong>Verizon</strong>'s Security Consulting Services–also known as "packaged"<br />
security services – help companies quickly improve their information security environment in an effective,<br />
cost-efficient way. <strong>Verizon</strong>’s suite of security consulting services offers complete, end-to-end security<br />
solutions, including:<br />
• Executive Security Briefing. Executive Security Briefings help organizations understand potential<br />
threats to their information assets, and the risks associated with today's computing environments.<br />
These 2-hour presentations are free, value-added services for the first 100 requests on the latest<br />
security threats and solutions. They are delivered to CIOs, VPs, and Directors.<br />
• Genuity Questionnaire. Before work on a security implementation can begin, <strong>Verizon</strong>/ Genuity<br />
administers a required, in-depth questionnaire to help establish a baseline of a company’s existing<br />
security systems, policies, and infrastructure. Because the questionnaire is fairly detailed and many<br />
companies do not have the in-house resources to complete it, <strong>Verizon</strong> provides a security consultant to<br />
assist the customer.<br />
• Vulnerability Testing Services. <strong>Verizon</strong> analyzes customers’ information "insecurity," which consists<br />
of three levels of testing:<br />
- Basic Vulnerability Testing Service. Includes port scans and vulnerability scanning tools; the<br />
latest security methodologies and technologies; and testing of components from external access<br />
points.<br />
- Intermediate Vulnerability Testing Service. Includes the basic testing service, plus consultation<br />
from system component experts who evaluate current security posture, develop guidelines and<br />
recommend improvements, and conduct high-level (basic) penetration testing.<br />
- Advanced Vulnerability Testing Service. Includes the basic assessment, plus comprehensive<br />
(detailed) penetration testing.<br />
<strong>Verizon</strong> provides a number of assessment services, including a Silver level and a more comprehensive<br />
Gold level assessment, as well as host, firewall, and HIPAA assessments, as described below:<br />
- Silver Level Assessment. The Silver Level Assessment includes a basic, external port scan,<br />
physical security review, documentation review, and network architecture diagram review. After<br />
<strong>Verizon</strong> security experts carefully analyze this information, they create a written report, hold a<br />
second meeting to discuss the report and customer security concerns, and finalize a comprehensive<br />
security plan.<br />
- Gold Level Assessment. This security assessment includes the basic components of the Silver<br />
Level Assessment, including a basic, external port scan, physical security review, documentation<br />
review, and network architecture diagram review. <strong>Verizon</strong> security experts carefully analyze this<br />
information, create a written report, hold a second meeting to discuss the report and customer<br />
security concerns, and finalize a comprehensive security plan. The Gold Level Assessment also<br />
includes:<br />
- An advanced, external port scan of the network to identify services.<br />
- A vulnerability scan of the external network (maximum of five public access servers).<br />
- Basic Phone (modem) sweep of the network to search for unauthorized modems connected to<br />
the network<br />
• Host Assessment. A Host Assessment determines how the operating system provides security for the<br />
network. The assessment also includes a review of physical security and how it relates to IT security,<br />
and a procedural review of security procedures in place. Key components of the assessment include:<br />
- An onsite physical security assessment and interview with physical security staff.<br />
- An automated Operating System assessment that gathers data about the operating system, its<br />
security features, settings, and service pack levels.<br />
- Assessment of up to 10 servers (5 external and 5 internal servers).<br />
- A review of the client’s security procedures.<br />
- Written report of findings with recommendations
• Firewall Assessment. <strong>Verizon</strong> Professional Security Services uses proven automated and manual<br />
processes to review customers’ Internet, Extranet, or Intranet firewall architectures to ensure that<br />
valuable assets are protected from attack. The assessment gathers data on operating system<br />
configurations, firewall administrative access, and firewall rule sets. The data are then compared<br />
against industry best practices, known security vulnerabilities, and compliance with any existing<br />
company security polices. The assessment culminates in a written report with findings and<br />
recommendations.<br />
• Security Policy Reviews. These are high-level assessments of an organization’s current policies,<br />
how they are disseminated to employees, and how they are enforced. The process begins with a<br />
customer interview, which results in an assessment of the current written policy.<br />
Please note that this review does not include the creation or modification of existing security policy, a<br />
service that <strong>Verizon</strong> offers as Security Policy Planning and Development. The final report will make<br />
recommendations about any deficiencies found during the review process.<br />
This review typically covers three major areas:<br />
- Logical Security. Includes system access control (i.e., log-in), password policy, software<br />
configuration and change control, anti-virus protection, acceptable use, data security, privacy, data<br />
availability, and data integrity.<br />
- Managerial Security. Includes security awareness training, personnel security, organizational<br />
structure (division of responsibility), policy enforcement, incident handling procedures, and<br />
separation of duties.<br />
- Physical Security. Includes building access control, restricted access to computer facilities (e.g.,<br />
server rooms), and computer location. Can also cover fire-suppression systems, facility<br />
construction, or air conditioning.<br />
• Security Policy Planning and Development. This service covers all of the basic<br />
analysis of the Security Policy Review (logical, managerial, physical security reviews),<br />
but goes beyond the review stage to provide businesses with a standard "Best Practices"<br />
Security Policy template. The template identifies, recommends, and implements<br />
appropriate security policy and policy-specified safeguards to help protect customers’<br />
information assets. Key components include:<br />
- Assessment of the full range of security policy and planning, including privacy, confidentiality,<br />
administration, Internet access, remote access, incident handling, audit requirements, roles and<br />
responsibilities, training and awareness, etc.<br />
- Draft Security Policy<br />
- Presentation of Draft Policy<br />
- Final Security Policy with high-level implementation plan<br />
• Technology Planning for Security Safeguards. This service helps customers select the<br />
best security solutions for their needs from a broad range of security consulting services.<br />
<strong>Verizon</strong> security consultants provide two (2) days of onsite consulting services to help<br />
customers select, design, and configure a robust security solution. <strong>Verizon</strong> offers<br />
technology planning services for the following security safeguards:<br />
- Firewalls - Two-Factor Authentication<br />
- Intrusion Detection <strong>Systems</strong> - PKI/ LDAP/ X.500<br />
- Virus Protection - Physical Security<br />
- Content Filtering - Biometrics<br />
- URL Filtering - RADIUS Servers<br />
- Encryption<br />
• Customer Training (Awareness, Executive Security, and IT Security). <strong>Verizon</strong> offers<br />
three types of training sessions for customers, which include Awareness Training,<br />
Executive Security Training (different from the pre-sales Executive Security Briefing),<br />
and IT Security Training.
- Security Awareness Training. Awareness Training follows the development of an information<br />
security policy. Once the security policy has been created and implemented, it should remain as<br />
the guideline for acceptable system use, and users should be informed of this through an<br />
awareness training session. <strong>Verizon</strong> offers awareness training sessions that:<br />
- Educate users about acceptable use of system assets<br />
- Explain the reasons why the company must protect its information assets<br />
- Review threats, including social engineering<br />
- Address the penalties for noncompliance<br />
- Executive Security (IT) Security Training. Executive-level training follows a complete<br />
investigative research of a customer's security network, and is intended to equip management with<br />
information on threats from the Internet, underground chat rooms, anarchy and hacktivists sites,<br />
etc., to determine if the customer is the subject of any potential attack.<br />
- IT Security Training. This training educates, informs, and guides IT personnel in planning,<br />
designing, implementing, and adhering to best security practices related to the need or<br />
environment.<br />
• Risk Assessment and Compliance Audits. <strong>Verizon</strong> has a unique set of skills and experience to ensure<br />
that customers receive the most comprehensive and cost-effective risk assessment and vulnerability<br />
analysis available. <strong>Verizon</strong> uses a custom-developed assessment methodology and tools to conduct<br />
comprehensive analysis of the security risks associated with the customer’s computing environment.<br />
Our security engineers know how the "bad guys" attack systems. When conducting assessments, our<br />
engineers think like hackers, and can exploit even the smallest of vulnerabilities. <strong>Verizon</strong> offers Basic<br />
and Advanced levels of Security Audits.<br />
• Computer Incident Response Team (CIRT) Retainer Program. <strong>Verizon</strong>’s CIRT and Cyber Crimes<br />
Unit have the experience and know-how to respond to today’s network intrusions and security events.<br />
The CIRT Retainer Program includes Incident Response Planning, CIRT Training, and CIRT<br />
Response. <strong>Verizon</strong> provides expert guidance in detection, containment, internal reporting, external<br />
disclosure, and investigation. Computer crime investigation and computer forensics are esoteric fields,<br />
and few individuals or corporations have the depth of experience as <strong>Verizon</strong>'s CIRT and Cyber Crimes<br />
Unit.<br />
Configuration Management of the Common Operating Environment<br />
<strong>Verizon</strong> MNS SiteWatch. MNS SiteWatch provides a scalable management and maintenance solution for<br />
customers’ data CPE. Letting <strong>Verizon</strong> take care of ensuring optimum performance of the data network lets<br />
customers focus their enterprise expertise on core business and strategic initiatives. The SiteWatch service<br />
offers three packaged solutions to meet customers' needs. These solutions offer a flexible set of feature<br />
choices, including fault detection and isolation, Web-based performance reports, and Move, add, and<br />
change (MAC) activities.<br />
All services include 24x7 proactive monitoring and combined data network management and maintenance<br />
capabilities. <strong>Verizon</strong> provides:<br />
• Fault Management. Fault detection and isolation, maintenance dispatch, carrier coordination, and<br />
web-based trouble ticketing. Four maintenance coverage options are available. This is positioned as<br />
enhanced maintenance.<br />
• Performance Management. Fault Management components, plus web-based performance reporting.<br />
Also included is a quarterly performance assessment.<br />
• Configuration Management. Performance Management components, plus software configuration<br />
capabilities, including MAC activities and software backup and restoral<br />
SiteWatch Configuration Management. SiteWatch Configuration Management offers customers end-toend<br />
WAN management solutions. This service offers all of the benefits of SiteWatch Fault Management<br />
and Performance Management, plus Configuration Management, to help ensure configuration data storage<br />
in case of device or configuration loss.<br />
SiteWatch Configuration Management helps customers maximize their network performance and minimize<br />
downtime by proactively monitoring their network and resolving all network faults for covered portions of
the network. <strong>Verizon</strong> engineers, experienced in troubleshooting network hardware, software, and<br />
LAN/WAN protocols, perform problem analysis and, if necessary, actively work with maintenance<br />
personnel to ensure quick solutions.<br />
SiteWatch Configuration Management offers analysis reports to help enhance network performance, and<br />
configuration data storage for backup purposes.<br />
<strong>Verizon</strong> monitors all network faults on devices covered by the customers' contracts. If faults occur, skilled,<br />
experienced <strong>Verizon</strong> engineers correct them.<br />
SiteWatch Configuration Management also collects reports on network performance, and stores<br />
configuration data for backup purposes. Quarterly, <strong>Verizon</strong> engineers analyze network reports and offer<br />
suggestions on how to improve network performance.<br />
<strong>Verizon</strong> <strong>Network</strong> Operations Centers (NOCs) store all configuration data for backup and change control<br />
configuration, on a regularly scheduled basis. In case of device or configuration loss, <strong>Verizon</strong> reloads the<br />
configuration as part of service restoration. Available services include:<br />
- <strong>Verizon</strong> MNS Web site access<br />
- Preferred vendor Web site access<br />
- Flexible CPE Maintenance Option<br />
- Software maintenance<br />
- <strong>Systems</strong> documentation<br />
- 24x7 phone support and troubleshooting<br />
- Web-based trouble ticketing<br />
- Verification of restorative action<br />
- Remote troubleshooting<br />
- Fault monitoring and detection<br />
- Carrier management<br />
- Customer notification<br />
- Web-based performance reports<br />
- Performance analysis<br />
- Configuration management.<br />
Voice Services<br />
<strong>Verizon</strong> offers a complete range of basic and advanced communications products and services to meet the<br />
voice, video, data, and IP-related needs of its customers. These include business phone lines, Internet<br />
access, data services, long distance, pay phones, enhanced calling services, telecom equipment, and more.<br />
Capabilities include:<br />
• Managed Voice<br />
Service (MVS)<br />
A solution that allows customers to let <strong>Verizon</strong> manage their voice<br />
communications. With the feature functionality of a PBX and the flexibility<br />
of Centrex, <strong>Verizon</strong> gives customers the ability to focus on their core business<br />
competencies. We can help by letting them use their capital to invest in their<br />
business, not in their communications network. We own (hold paper, pay<br />
taxes) and maintain the network, and the customer pays a simple monthly rate<br />
per port for their PBX service, maintenance, and Moves, adds, and changes<br />
(MAC). As technology evolves, customers have the ability to renegotiate<br />
their contracts to take advantage of new communications products and<br />
services.<br />
• WAN Solutions Private Line, Frame Relay, ATM, SONET, DWDM, Gigabit Ethernet, (Local<br />
and Long Distance service)<br />
• <strong>Network</strong> Integration Integration, Consulting, and Managed Services<br />
• IP Solutions Dedicated and Dial Internet Access; Web Development, Hosting, and<br />
Management; Security Services; and Messaging<br />
• LAN Solutions Intelligent Wiring, Routers, Hubs and Switches, Installation, Maintenance,<br />
and Repair<br />
• Voice Access and<br />
Transport<br />
• Voice Switching<br />
Solutions<br />
Local, DID/DOD, Integrated Services Digital <strong>Network</strong> (ISDN) PRI/BRI,<br />
IntraLATA and InterLATA Toll, Voice over IP (VoIP), and Value Added<br />
Services<br />
Centrex, PBX, KSU, IP-PBX, Voice Processing, I/M&R, Converged CPE
Please note that installation options vary depending upon location, equipment manufacturer, and type.<br />
Locations such as Texas and the tri-state area also have a local <strong>Verizon</strong> installation/maintenance<br />
organization option, as well as National-based service.<br />
Video Teleconferencing<br />
Business travel has decreased dramatically. Videoconferencing provides the real-time experience of a<br />
physical meeting. <strong>Verizon</strong> can offer all of the video CPE–camera, monitor, codec, audio, and system<br />
control device–as well as the network, for a total videoconferencing solution.<br />
Infrastructure and Cable Installation<br />
<strong>Verizon</strong> Enterprise <strong>Network</strong> Consulting Services. <strong>Verizon</strong>'s Enterprise <strong>Network</strong> Consulting Services are<br />
value-added planning services designed to assist customers in the strategic planning and design of their<br />
enterprise networks. From wide, local, and metropolitan area networking, to remote access, to address<br />
management, to convergence, <strong>Verizon</strong> experts are prepared to assist customers in any of the following<br />
disciplines:<br />
• <strong>Network</strong> Architecture & Planning. <strong>Verizon</strong> <strong>Network</strong> Architecture and Planning services help<br />
enterprise customers closely align their technology initiatives with their business objectives. Utilizing<br />
a phased approach, <strong>Verizon</strong> engineers develop an architecture and technology roadmap to guide<br />
customers from legacy to next-generation networks in support of their business objectives. <strong>Verizon</strong><br />
engineers start by conducting a high-level assessment to gain an understanding of the current network.<br />
Next, through an interview process and review of customer planning documents, architectural goals are<br />
defined and prioritized. In the next phase, architecture alternatives are defined and evaluated, and a<br />
recommendation developed. Lastly, a transition plan to guide the customer through the migration is<br />
assembled. An executive briefing describing the process and results is provided to the customer.<br />
• <strong>Network</strong> Design. A comprehensive design should not be underestimated in any construction or<br />
development effort, whether it is the construction of a new building or the development of a new<br />
product. Enterprise networks are no different. To implement a scalable, reliable, robust network to<br />
meet business objectives and maximize return on investment, a formal network design is a must. It has<br />
been common in the past to pull together network designs without thorough requirements gathering,<br />
and almost as a result of technology selection, rather than a prerequisite, often at little or no cost.<br />
However, this lack of emphasis has resulted in networks that do not fulfill business requirements and<br />
do not meet expectations of technology executives.<br />
<strong>Verizon</strong> <strong>Network</strong> Design Services assists enterprise clients in developing detailed network<br />
specifications and implementation tactics, to serve as the basis for scalable, robust, and reliable<br />
network solutions. These specifications for the physical, logical, and operational infrastructure are<br />
developed with consideration of how the new technology will integrate into the existing network, and<br />
with an eye to ensuring that the design supports the architecture and technology roadmap. Maximizing<br />
the return on investment starts with a solid foundation in architecture, and is only possible with a<br />
comprehensive network design.<br />
• <strong>Network</strong> Assessment Services. <strong>Network</strong> Assessment services improves the return on IT investment<br />
by maximizing the efficiency of the network infrastructure, and planning for future growth in a logical<br />
and disciplined manner. Whether the assessment focuses on network inventory, performance,<br />
reliability, availability, or all of the above, <strong>Verizon</strong> engineers utilize proven methodologies and stateof-the-art<br />
tools to ensure a meticulous audit of the enterprise network according to the objectives<br />
identified at the onset of the engagement. The <strong>Network</strong> Assessment is often the starting point for a<br />
new technology implementation initiative, and ensures the accuracy of the planning baseline, such that<br />
new initiatives are built on a solid foundation. The focus of the network assessment typically includes<br />
any combination of the following areas:<br />
- WAN/ MAN/ LAN topologies<br />
- <strong>Network</strong> operating systems, gateways, protocols<br />
- General throughput/ capacity<br />
- Bottlenecks, problem area identification<br />
- <strong>Network</strong> management capabilities<br />
- Operations and Administration procedures
- Redundancy and identification of single points of failure<br />
- External Communication Partners<br />
<strong>Verizon</strong> network consultants provide expertise in the following major networking disciplines:<br />
- Wide, metropolitan, and local area networking<br />
- Voice, video, and data convergence<br />
- Internet connectivity and Firewall technology planning<br />
- Content delivery networking<br />
- Wireless networking<br />
- Remote access infrastructure planning<br />
- Address Management. Directory services, application-based QoS and policy management<br />
• Wide Area <strong>Network</strong> Monitoring Support. <strong>Verizon</strong> also provides WAN monitoring support from our<br />
network control centers. Our communications links are provided through <strong>Verizon</strong>’s existing backbone<br />
network. Communications links to the existing customer WAN are through one or more dedicated<br />
T1s, with an equal number of redundant T1s for backup.<br />
Software Consultation and Planning<br />
Please refer to the <strong>Verizon</strong> Enterprise <strong>Network</strong> Consulting Services discussion in Section 2.7, Infrastructure<br />
and Cable Installation, of this Capability Statement. <strong>Verizon</strong> provides commercial off-the-shelf integration,<br />
custom software development, and lifecycle support services, both in-house and through third-party<br />
teaming arrangements.<br />
Engineering Solutions and Program Management<br />
<strong>Verizon</strong> is adept at engineering comprehensive and innovative technical solutions to meet customer needs<br />
for IT/telecom technology. <strong>Verizon</strong>'s IT solutions will have the flexibility to minimize risk, and provide<br />
best value.<br />
MANAGEMENT (A1 – A2)<br />
A1. Program Manager<br />
A2. Project Manager<br />
A3. Project Administrator<br />
LABOR CATAGORIES<br />
TECHNOLOGY (A15 – A22)<br />
A15. Chief Technologist<br />
A16. Principal Technologist<br />
A17. Divisional Technologist<br />
A18. Senior Technical Professional<br />
A19. Technical Professional<br />
A20. Staff Technical Professional<br />
A21. Senior Project Administrator<br />
A22. Senior Data Control Specialist<br />
B. NETWORK SERIES (B1-B22)<br />
B1. Senior <strong>Network</strong> Engineer<br />
B2. <strong>Network</strong> Engineer<br />
B3. Junior <strong>Network</strong> Engineer<br />
B4. Senior <strong>Systems</strong> Engineer<br />
B5. <strong>Systems</strong> Engineer<br />
B6. Junior <strong>Systems</strong> Engineer
B7. Sustaining Engineer<br />
B8. Junior Sustaining Engineer<br />
B9. Senior Sales Engineer<br />
B10. Sales Engineer<br />
B11. <strong>Network</strong> Security Project Manager<br />
B12. <strong>Network</strong> Security Senior Consultant<br />
B13. Senior <strong>Network</strong> Security Engineer<br />
B14. <strong>Network</strong> Security Engineer<br />
B15. Junior <strong>Network</strong> Security Engineer<br />
B16. Senior <strong>Network</strong> Security Analyst<br />
B17. <strong>Network</strong> Security Analyst<br />
B18. Junior <strong>Network</strong> Security Analyst<br />
B19. Senior Technical Writer, <strong>Network</strong> Security<br />
B20. Technical Writer, <strong>Network</strong> Security<br />
B21. <strong>Network</strong> Manager<br />
B22. <strong>Network</strong> Administrator<br />
C. RESERVED<br />
D. COMPUTER OPERATIONS SERIES (D1-D6)<br />
D1. Reserved<br />
D2. Computer <strong>Systems</strong> Analyst<br />
D3. Applications Engineer<br />
D4. Operations Manager<br />
D5 Reserved<br />
D6. <strong>Systems</strong> Operator<br />
E. TECHNICIAN SERIES (E1-D2)<br />
E1. Reserved<br />
E2. Communications Technician<br />
F. SUPPORT SERIES (F1-F6)<br />
F1. Sr. Tech Writer<br />
F2. Tech Writer<br />
F3. Administrative Support/ Graphics Specialist<br />
F4. Help Desk Manager<br />
F5. Help Desk Specialist<br />
F6. Technical Typist
SKILL CATEGORY REQUIREMENTS<br />
1. QUALIFICATION REQUIREMENTS. To perform on this schedule, contractor personnel must meet the<br />
minimum requirement for the skill categories described herein. In addition to the total and specialized<br />
experience defined in the skill categories, specific areas of required expertise may be further defined in a<br />
Government task request.<br />
2. TASK LEADER. Where the size of a task order warrants, a task leader shall be named for the task order<br />
by BBN to manage BBN’s efforts.<br />
3. SUBSTITUTION OF EDUCATION FOR EXPERIENCE. A Bachelor's degree or higher may be<br />
substituted for the general and specialized experience for those labor categories requiring a high school<br />
diploma. Substitution shall be approved by the COTR.<br />
4. SUBSTITUTION OF EXPERIENCE FOR EDUCATION. Substitution of experience for education is<br />
not allowed for some of the categories. The restriction has been identified within the category descriptions<br />
where it applies. The substitution rate for categories with no restriction will be two(2) years of experience<br />
for one(1) year of education unless otherwise specified. Substitution shall be approved by the COTR.<br />
5. MINIMUM/GENERAL EXPERIENCE & EDUCATION FORMAT. The minimum experience and<br />
educational requirements for each skill category are as follows:<br />
(1) Experience Requirements.<br />
(a) Total Experience. Minimum years of general experience in information systems technology<br />
(b) Specialized Experience. Minimum specific experience required directly relates to the particular<br />
skill category and level. The experience is not in addition to but is a part of the general experience<br />
required in paragraph a. Required experience may be further defined in the task order.<br />
(c) Task Leader. Indicates this category may serve as a task leader on one or more task orders.<br />
Management experience will be required since the category qualifications do not require<br />
managerial experience. Task leaders must have supervisory or project leader experience. This<br />
experience is not in addition to the experience requirements for the skill category. Project leader<br />
experience is experience that demonstrates an individual's ability to accomplish projects/tasks<br />
through others.<br />
(2) Functional Responsibility. This section will contain a description of duties representative of the<br />
position.<br />
(3) Education and Other Requirements. Minimum educational requirements needed to qualify for the<br />
position. The COTR may approve substitutions of experience for education if the COTR determines<br />
the experience is superior in nature and provides the skills at a level necessary to successfully perform<br />
the duties of the position.<br />
(a) Substitution. Permitted substitutions or a statement that substitutions not allowed for this category.
A. MANAGEMENT (A1-A3)<br />
These positions provide contractor management, senior level managers, and technical support for complex<br />
analysis tasks in the area of information technology. Such personnel will interface directly with<br />
government personnel in day-to-day management.<br />
A1: PROGRAM MANAGER<br />
(1) Experience requirements:<br />
(a) Total Experience. Fifteen (15) years of progressive experience in the development of systems<br />
in broad-based information technology (IT) settings involving the use of contemporary tools and<br />
techniques for information systems development.<br />
(b) Specialized Experience. Ten (10) years of specific experience in project development from<br />
inception to deployment, demonstrated ability to provide guidance and direction in tasks of<br />
varying levels of size and scope of effort, proven expertise in the management and control of<br />
funds and resources, demonstrated capability in managing multi-task contracts of this type and<br />
complexity envisioned for this schedule<br />
(2) Functional Responsibility. Serves as the contractor's single program manager for a large, complex<br />
task order (or a group of task orders affecting the same common/standard/migration system), and shall<br />
be the contractor's authorized interface with the Government authorized representative, government<br />
management personnel and customer agency representatives. Responsible for formulating and<br />
enforcing work standards, assigning contractor schedules, reviewing work discrepancies, supervising<br />
contractor personnel and communicating policies, purposes, and goals of the organization to<br />
subordinates. Shall be responsible for the overall contractor’s performance. Plans and supervises<br />
multiple projects and/or task orders involving complex information systems software development.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering, Business or other<br />
related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Master of Sciences degree (in the fields described in section b above): thirteen (13)<br />
years general experience of which at least nine (9) years specialized experience is required<br />
– With a Ph.D. (in the fields described in b above) twelve (12) years general experience of<br />
which at least eight (8) years must be specialized experience<br />
A2: PROJECT MANAGER<br />
(1) Experience requirements:<br />
(a) Total Experience. Twelve (12) years of progressive experience in the development of systems<br />
in broad-based information technology (IT) settings involving the use of contemporary tools and<br />
techniques for information systems development; may work under the guidance of a Program<br />
Manager<br />
(b) Specialized Experience. Nine (9) years of specific experience in project development from<br />
inception to deployment, demonstrated ability to provide guidance and direction in tasks of<br />
varying levels of size and scope of effort, proven expertise in the management and control of<br />
funds and resources, demonstrated capability in managing multi-task contracts of this type and<br />
complexity envisioned for this schedule
(2) Functional Responsibility. Serves as the project manager for a large, complex task order (or a group<br />
of task orders affecting the same common/standard/migration system) and shall assist the Program<br />
Manager in working with the Government’s authorized representative, the task order-level COTR(s),<br />
government management personnel and customer agency representatives. Under the guidance of the<br />
Program Manager, responsible for the overall management of the specific task order(s) and insuring<br />
that the technical solutions and schedules in the task order are implemented in a timely manner.<br />
Performs enterprise wide horizontal integration planning and interfaces to other functional systems.<br />
Plans and supervises multiple projects and/or task orders involving complex information systems<br />
software development<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering, Business or other<br />
related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Masters degree (in the fields described in section b above): ten (10) years general<br />
experience of which at least seven (7) years specialized experience is required<br />
– With a Ph.D. (in the fields described in b above) eight (8) years general experience of which<br />
at least six (6) years must be specialized experience<br />
A3. PROJECT ADMINISTRATOR<br />
(1) Experience Requirements:<br />
Four (4) or more years experience, preferably in finance, contract administration, database<br />
management or administration of technical projects<br />
(2) Functional Responsibility. Maintains computer and manual files regarding program costs and<br />
schedules , and other administrative matters. Analyzes program cost/schedule performance, and<br />
prepares reports for Program Managers. Alerts Program Managers to significant variances or other<br />
extraordinary items. Reviews reports submitted by technical staff, and initiates corrective procedures<br />
when errors are suspected. Provides data needed for estimating expenses, budgets, contractual<br />
deliverables<br />
(3) Education Requirements. BS/BA or equivalent experience<br />
TECHNOLOGY SERIES (A15-A23)<br />
A15: CHIEF TECHNOLOGIST<br />
(1) Experience requirements:<br />
(a) Total Experience. Seventeen (17) years of experience in providing expert, independent services<br />
and leadership in specialized technical areas. Provides expertise on an as needed basis to all task<br />
assignments while coordinating with team members to ensure the problem has been properly<br />
defined and that the solution satisfied requirements. Possesses requisite knowledge and expertise<br />
so recognized in the professional community that the Government is able to qualify the individual<br />
as an expert in the field for a specific Task Assignment. Demonstrates exceptional oral and written<br />
communications skills<br />
(b) Specialized Experience. Thirteen (13) years of specific experience is required while<br />
demonstrating progressive accomplishments as an expert in large and complex information<br />
technology systems implementations. Expertise is applied across multiple information technology<br />
platforms and the integration of diverse architectures. Must demonstrate the ability to work
independently and lead large technologically oriented teams focused on a specific problem or<br />
requirements set. Demonstrates exceptional oral and written communications skills<br />
(2) Functional Responsibility. Serves as a technology expert in the architecture and development of<br />
large systems requiring state-of-art technology that is based on complex engineering techniques and/or<br />
processes. Establishes system requirements using analysis of enterprise-wide or large scale information<br />
systems to determine critical features and establishing performance models to ensure the viability of<br />
the required tasks, the interrelationships of the tasks, and that a recommended solution will meet all<br />
requirements in an effective manner. Designs systems architectures that include software, hardware,<br />
and communications to support the total set of system requirements as well as provide for present and<br />
future cross-functional requirements and interfaces. Ensures these systems are compatible and in<br />
compliance with the standards for open systems architectures, the Open <strong>Systems</strong> Interconnection (OSI)<br />
and International Standards Organization (ISO) reference models, and profiles of standards - such as<br />
Institute of Electrical and Electronic Engineers (IEEE) Open <strong>Systems</strong> Environment (OSE) reference<br />
model - as they apply to the implementation and specification of Information Management (IM)<br />
solution of the application platform, across the application program interface (API), and the external<br />
environment/software application. Ensures that the common operating environment is compliant with<br />
agency standards. Evaluates analytically and systematically problems of work flows, organization, and<br />
planning and develops appropriate corrective action.<br />
(3) Education and Other Requirements. A Master of Science degree from an accredited university with<br />
a major in Engineering, Computer Science or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Ph.D. (in the fields described in b above) fourteen (14) years general experience of<br />
which at least ten (10) years must be specialized experience<br />
– With a Bachelor of Science degree in Engineering, Computer Science or other related<br />
scientific or technical discipline and twenty (20) years general experience of which at least<br />
fifteen (15) years must be specialized experience, a Masters degree is not required<br />
A16: PRINCIPAL TECHNOLOGIST<br />
(1) Experience requirements:<br />
(a) Total Experience. Fifteen (15) years of experience in providing expert, independent services<br />
and leadership in specialized technical areas. Provides expertise on an as needed basis to all task<br />
assignments while coordinating with team members to ensure the problem has been properly<br />
defined and that the solution satisfied requirements. Possesses requisite knowledge and expertise<br />
so recognized in the professional community that the Government is able to qualify the individual<br />
as an expert in the field for a specific Task Assignment. Demonstrates exceptional oral and<br />
written communications skills<br />
(b) Specialized Experience. Twelve (12) years of specific experience is required while<br />
demonstrating progressive accomplishments as an expert in large and complex information<br />
technology systems implementations. Expertise is applied across multiple information technology<br />
platforms and the integration of diverse architectures. Must demonstrate the ability to work<br />
independently or under only general direction<br />
(2) Functional Responsibility. Serves as a technology expert in the architecture and development of<br />
large systems requiring state-of-art technology that is based on complex engineering techniques and/or<br />
processes. Establishes system requirements using analysis of enterprise-wide or large scale information<br />
systems to determine critical features and establishing performance models to ensure the viability of<br />
the required tasks, the interrelationships of the tasks, and that a recommended solution will meet all<br />
requirements in an effective manner. Designs systems architectures that include software, hardware,
and communications to support the total set of system requirements as well as provide for present and<br />
future cross-functional requirements and interfaces. Ensures these systems are compatible and in<br />
compliance with the standards for open systems architectures, the Open <strong>Systems</strong> Interconnection (OSI)<br />
and International Standards Organization (ISO) reference models, and profiles of standards - such as<br />
Institute of Electrical and Electronic Engineers (IEEE) Open <strong>Systems</strong> Environment (OSE) reference<br />
model - as they apply to the implementation and specification of Information Management (IM)<br />
solution of the application platform, across the application program interface (API), and the external<br />
environment/software application. Ensures that the common operating environment is compliant with<br />
agency standards. Evaluates analytically and systematically problems of work flows, organization, and<br />
planning and develops appropriate corrective action<br />
(3) Education and Other Requirements. A Master of Science degree from an accredited university with<br />
a major in Engineering, Computer Science or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Ph.D. (in the fields described in b above) twelve (12) years general experience of<br />
which at least nine (9) years must be specialized experience<br />
– With a Bachelor of Science degree in Engineering, Computer Science or other related<br />
scientific or technical discipline and seventeen (17) years general experience of which at<br />
least thirteen (13) years must be specialized experience, a Masters degree is not required<br />
A17: DIVISIONAL TECHNOLOGIST<br />
(1) Experience requirements:<br />
(a) Total Experience. Twelve (12) years of experience in providing expert, independent services<br />
and leadership in specialized technical areas. Provides expertise on an as needed basis to all task<br />
assignments while coordinating with team members to ensure the problem has been properly<br />
defined and that the solution satisfied requirements. Possesses requisite knowledge and expertise<br />
to be recognized as a specialist in the field for a specific Task Assignment<br />
(b) Specialized Experience. Ten (10) years of specific experience is required while demonstrating<br />
a progressive accomplishment as an expert in large and implementing complex information<br />
technology systems. Expertise is applied across multiple information technology platforms and<br />
the integration of diverse architectures. Must demonstrate the ability to work independently or<br />
under only general direction<br />
(2) Functional Responsibility. Serves as a technology expert in the architecture and development of<br />
large systems requiring state-of-art technology that is based on complex engineering techniques and/or<br />
processes. Establishes system requirements using analysis of enterprise-wide or large scale information<br />
systems to determine critical features and establishing performance models to ensure the viability of<br />
the required tasks, the interrelationships of the tasks, and that a recommended solution will meet all<br />
requirements in an effective manner. Designs systems architectures that include software, hardware,<br />
and communications to support the total set of system requirements as well as provide for present and<br />
future cross-functional requirements and interfaces. Ensures these systems are compatible and in<br />
compliance with the standards for open systems architectures, the Open <strong>Systems</strong> Interconnection (OSI)<br />
and International Standards Organization (ISO) reference models, and profiles of standards - such as<br />
Institute of Electrical and Electronic Engineers (IEEE) Open <strong>Systems</strong> Environment (OSE) reference<br />
model - as they apply to the implementation and specification of Information Management (IM)<br />
solution of the application platform, across the application program interface (API), and the external<br />
environment/software application. Ensures that the common operating environment is compliant with<br />
agency standards. Evaluates analytically and systematically problems of work flow, organization, and<br />
planning and develops appropriate corrective action
(3) Education and Other Requirements. A Master of Science degree from an accredited university with<br />
a major in Engineering, Computer Science or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Ph.D. (in the fields described in b above) ten (10) years general experience of which<br />
at least nine (9) years must be specialized experience.<br />
– With a Bachelor of Science degree in Engineering, Computer Science or other related<br />
scientific or technical discipline and fifteen (15) years general experience of which at least<br />
eleven (11) years must be specialized experience, a Masters degree is not required<br />
A18: SENIOR TECHNICAL PROFESSIONAL<br />
(1) Experience requirements:<br />
(a) Total Experience. Twelve (12) years of progressive experience in the development of systems<br />
in broad-based information technology (IT) settings providing in-depth subject matter expertise<br />
and an ability to translate these into system requirements, systems architecture, and research,<br />
development, and test tasks. Possesses requisite knowledge and expertise to be recognized as a<br />
specialist in the field for a specific Task Assignment<br />
(b) Specialized Experience. Ten (10) years of superior functional knowledge of task order specific<br />
requirements, or developing functional requirements for complex integrated ADP systems. Must<br />
demonstrate the ability to work independently or under only general direction<br />
(2) Functional Responsibility. At a large-scale information system or enterprise-wide level, analyze<br />
user needs to determine functional and cross-functional requirements. Performs functional allocation<br />
to identify required tasks and their interrelationships. Applies business process improvement practices<br />
to re-engineer methodologies/principles and business process modernization projects. Applies, as<br />
appropriate, activity and data modeling, transaction flow analysis, internal control and risk analysis and<br />
modern business methods and performance measurement techniques. Assist in establishing standards<br />
for information systems procedures. Develops and applies organization-wide information models for<br />
use in designing and building integrated, shared software and database management systems.<br />
Constructs sound, logical business improvement opportunities consistent with corporate Information<br />
Management guiding principles, cost savings, and open system architecture objectives<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited university<br />
with a major in Computer Science, Engineering, or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Ph.D. (in the fields described in b above) six (6) years general experience of which<br />
at least four (4) years must be specialized experience<br />
– With a Master of Sciences degree (in the fields described in section b above): nine (9) years<br />
general experience of which at least six (6) years specialized experience is required<br />
A19: TECHNICAL PROFESSIONAL<br />
(1) Experience requirements.<br />
(a) Total Experience. Ten (10) years of progressive experience in systems analysis and computer<br />
programming in highly complex and broad-based information technology (IT) settings providing<br />
in-depth subject matter expertise and an ability to translate these into system requirements,
systems architecture, and research, development and test tasks. In depth experience in the use of<br />
contemporary communications systems, computer hardware, relational data base technologies, and<br />
high order programming languages<br />
(b) Specialized Experience. Eight (8) years of superior functional knowledge of task order specific<br />
requirements, or developing functional requirements for complex integrated ADP systems. Should<br />
have proven expertise in the management and control of funds and resources and demonstrated<br />
capability in managing multi-task task orders. Must demonstrate the ability to work independently<br />
or under only general direction<br />
(2) Functional Responsibility. At a large-scale complex information system or enterprise-wide level,<br />
analyze user needs to determine functional and cross-functional requirements. Performs functional<br />
allocation to identify required tasks and their interrelationships. Applies business process improvement<br />
practices to re-engineer methodologies/principles and business process modernization projects.<br />
Applies, as appropriate, activity and data modeling, transaction flow analysis, internal control and risk<br />
analysis and modern business methods and performance measurement techniques. Assist in<br />
establishing standards for information systems procedures. Develops and applies organization-wide<br />
information models for use in designing and building integrated, shared software and database<br />
management systems. Constructs sound and logical improvement opportunities consistent with<br />
corporate Information Management guiding principles, cost savings, and open system architecture<br />
objectives<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited university<br />
with a major in Computer Science, Engineering, or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Ph.D. (in the fields described in b above) three (3) years specialized<br />
– With a Master of Sciences degree (in the fields described in section b above): six (6) years<br />
general experience of which at least four (4) years specialized experience is required<br />
A20: STAFF TECHNICAL PROFESSIONAL<br />
(1) Experience requirements:<br />
(a) Total Experience. Eight (8) years of progressive experience in systems analysis and computer<br />
programming in highly complex and broad-based information technology (IT) settings involving<br />
the use of contemporary communications systems, computer hardware, relational data base<br />
technologies, and high order programming languages<br />
(b) Specialized Experience. Six (6) years of specific experience in large, complex information<br />
systems software development projects. Must have demonstrated expertise through effective use<br />
of state-of-the-art development tools and models. Must have proven expertise in the effective use<br />
of highly specialized personnel resources and a demonstrated capability in managing multi-task<br />
activities simultaneously<br />
(2) Functional Responsibility. At a large-scale complex information system or enterprise-wide level,<br />
analyze user needs to determine functional and cross-functional requirements. Performs functional<br />
allocation to identify required tasks and their interrelationships. Applies business process improvement<br />
practices to re-engineer methodologies/principles and business process modernization projects.<br />
Applies, as appropriate, activity and data modeling, transaction flow analysis, internal control and risk<br />
analysis and modern business methods and performance measurement techniques. Assist in<br />
establishing standards for information systems procedures. Develops and applies organization-wide<br />
information models for use in designing and building integrated, shared software and database<br />
management systems. Constructs sound and logical improvement opportunities consistent with
corporate Information Management guiding principles, cost savings, and open system architecture<br />
objectives.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited university<br />
with a major in Computer Science, Engineering, or other related scientific or technical discipline.<br />
(a) Substitution.<br />
– With a Master of Sciences degree (in the fields described in section b above): five (5) years<br />
general experience of which at least four (4) years specialized experience is required<br />
A21: SENIOR PROJECT ADMINISTRATOR<br />
(1) Experience Requirements<br />
(a) Total Experience. Six (6) years progressive experience in IS/ADP systems administration<br />
(b) Specialized Experience. Three (3) years intensive and progressive specific experience in the<br />
administration of complex data systems<br />
(2) Functional Responsibility. Specifies proper types of files organization, indexing methods, and<br />
security procedures. Advises project teams on the design of complex databases (e.g., schema and subschema<br />
details). Defines specialized aspects of user's data base administrator documentation. Performs<br />
detailed comparisons of various data base systems. Performs duties in a complex, distributed,<br />
heterogeneous computing environment, which may involve different types of hardware platforms,<br />
operating systems applications, and network environments. Provides expertise in data storage systems.<br />
Performs administration tasks (installing, maintaining, monitoring, recovering, rebuilding, upgrading,<br />
patching and performance tuning). Implements software solutions for performance enhancement,<br />
operator interface, and increased user capability. Augments other skill categories by providing unique<br />
IS/ADP systems administration knowledge in areas that require in-depth current knowledge of a<br />
specialized IS discipline. Such specialized knowledge can only be achieved through intensive,<br />
extensive, and continuous application of the specialty at a level exceeding that of the more general and<br />
broad based IS requirements of the skill category series<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited university<br />
with a major in Computer Science, Engineering, or other related scientific or technical discipline<br />
(a) Substitution:<br />
– With a Master of Sciences degree (in the fields described in section b above): four (4) years<br />
general experience of which at least two (2) years specialized experience is required<br />
A22: SENIOR DATA CONTROL SPECIALIST<br />
(1) Experience requirements:<br />
(a) Total Experience. Five (5) years progressive experience in the management Data Base <strong>Systems</strong><br />
and their administration<br />
(b) Specialized Experience. Three (3) years intensive and progressive specific experience in the<br />
administration of complex data systems<br />
(2) Functional Responsibility. Performs assigned portions of managing the data input into complex<br />
information systems. Analyzes and administers data for both the developing team and the customer.<br />
Handles daily administrative tasks, produces and edits technical reports based on data system<br />
processing, monitors use of data and performs updates as required. Participates in all phases of system
development with emphasis on the data collection, input, documentation, and acceptance phases.<br />
Designs and prepares technical reports and related documentation, and makes charts and graphs to<br />
record results<br />
(3) Education and Other Requirements. An Associate's degree from an accredited college or university<br />
in Computer Science, Engineering or other related scientific or technical discipline<br />
(a) Substitution. Substitution not allowed for this category.<br />
B. NETWORK SERIES (B1-B22)<br />
These positions provide contractor management, senior level managers, and technical support for network<br />
engineering tasks in the area of information technology. Such personnel will interface directly with<br />
government personnel in day-to-day management.<br />
B1: Senior <strong>Network</strong> Engineer<br />
(1) Experience Requirements:<br />
(a) Total Experience. Five (5) years or more of progressive experience in planning, designing and<br />
analyzing data or telecommunications networks. This experience must demonstrate a working<br />
knowledge of Ethernet, FDDI, frame relay and ATM, and a working knowledge of operating<br />
systems and protocols such as Novell, NT, UNIX, SNA and TCP/IP. Must have experience with<br />
network analysis/management tools and techniques and be familiar with PCs in a client server<br />
environment. Must be familiar with IT and long distance and local carrier management.<br />
Knowledge of computer languages such as C, C++, SQL is a plus. Supervisory or project leader<br />
experience is also required.<br />
(2) Functional Responsibility. Responsible for the design and implementation of data communications<br />
or telecommunications networks. Plans and monitors the installation of communication circuits and<br />
recommends enhancements. Manages and monitors LANs and associated equipment (e.g., bridges,<br />
routers, hubs, modem pools, gateways, etc.). Analyzes interface requirements between WANs and<br />
other computer networks. Analyzes network characteristics (e.g., traffic, connect time, transmission<br />
speeds, packet sizes and throughput). Conducts short and long term planning to meet communications<br />
system requirements.<br />
3) Education and Other Requirements. A Bachelor of Science or Masters of Science degree from an<br />
accredited college or university with a major in Computer Science, Information <strong>Systems</strong>, Engineering<br />
other related scientific or technical discipline.<br />
4) Substitution. Six (6) or more years direct network experience, Bachelor of Science or Bachelor of<br />
Arts degree from an accredited college or university with a major in a non-technical discipline.<br />
Demonstrated network aptitude and depth of overall network familiarity based upon experience.<br />
B2: <strong>Network</strong> Engineer<br />
(1) Experience Requirements.<br />
(a) Total Experience. Two (2) to five (5) years network experience<br />
(2) Functional Responsibility. Duties are performed under the supervision of a senior engineer or<br />
technical project manager. Assists in the design and implementation of LAN/WANs using hub and<br />
router technology. Performs hardware/software analyses to provide comparative data of performance<br />
characteristics and suitability within the existing systems environment. Prepares trade-off studies and
evaluations for vendor equipment. Assists in generating network monitoring and performance reports<br />
for LAN/WANs utilization studies. Recommends network design changes/enhancements for improved<br />
system availability and performance. Knowledge includes demonstrated capability in at least one<br />
primary network element, such as operating systems, platforms or protocols<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering or other related<br />
scientific or technical discipline<br />
a) Substitution. Three (3) to six (6) years direct network experience, Bachelor of Science or<br />
Bachelor of Arts degree from an accredited college or university with a major in a non-technical<br />
discipline. Demonstrated network aptitude based upon experience<br />
B3: Junior <strong>Network</strong> Engineer<br />
(1) Experience Requirements:<br />
(a) Total Experience. Minimum required. Entry level position. Zero to two (2) years network<br />
experience<br />
(2) Functional Responsibility. Duties are performed under the direct guidance of a senior engineer.<br />
Assists in the design and implementation of LAN/WANs using hub and router technology. Performs<br />
hardware/software analyses to provide comparative data of performance characteristics and suitability<br />
within the existing systems environment. Assists in generating network monitoring and performance<br />
reports for LAN/WANs utilization studies. Provides input for network design changes/enhancements<br />
for improved system availability and performance.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering or other related<br />
scientific or technical discipline.<br />
(a) Substitution. One (1) to three (3) years direct network experience, Bachelor of Science or<br />
Bachelor of Arts degree from an accredited college or university with a major in a non-technical<br />
discipline. Demonstrated network aptitude based upon experience.<br />
B4: Senior <strong>Systems</strong> Engineer<br />
(1) Experience Requirements:<br />
a) Total Experience. Five (5) years or more of intensive and progressive specific experience in<br />
planning, designing and analyzing telecommunications networks. This experience must include<br />
demonstrated knowledge of Ethernet, FDDI, frame relay and ATM, and a working knowledge of<br />
operating systems and protocols such as Novell, NT, UNIX, SNA and TCP/IP. Must have<br />
experience with network analysis/management tools and techniques and be familiar with PCs in a<br />
client server environment. Must be familiar with IT and long distance and local carrier<br />
management. Demonstrated ability as a supervisor or project leader essential. Highest skills in<br />
written and oral communications needed. Knowledge of computer languages such as C, C++,<br />
SQL, HTML, is a strong plus. Supervisory or project leader experience is also essential.<br />
(2) Functional Responsibility. Assists in the design and implementation of LAN/WANs using hub and<br />
router technology. Performs hardware/software analyses to provide comparative data of performance<br />
characteristics and suitability within the existing systems environment. Prepares trade-off studies and<br />
evaluations for vendor equipment. Assists in generating network design changes/enhancements for<br />
improved system availability and performance.
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering or other related<br />
scientific or technical discipline.<br />
a) Substitution. Six (6) or more years direct network experience, Bachelor of Science or Bachelor<br />
of Arts degree from an accredited college or university with a major in a non-technical discipline.<br />
Demonstrated system-level network aptitude based upon experience. Demonstrated technical and<br />
project leadership ability.<br />
B5: <strong>Systems</strong> Engineer<br />
(1) Experience Requirements:<br />
a) Total Experience. Three (3) to five (5) years of intensive and progressive specific experience in<br />
planning, designing and analyzing telecommunications networks. This experience must include<br />
demonstrated knowledge of Ethernet, FDDI, frame relay and ATM, and a working knowledge of<br />
operating systems and protocols such as Novell, NT, UNIX, SNA and TCP/IP. Must be familiar<br />
with network analysis / management tools and techniques and be familiar with PCs in a client<br />
server environment.<br />
(2) Functional Responsibility. Assists in the design and implementation of LAN/WANs using hub and<br />
router technology. Performs hardware/software analyses to provide comparative data of performance<br />
characteristics and suitability within the existing systems environment. Prepares trade-off studies and<br />
evaluations for vendor equipment. Assists in generating network monitoring and performance reports<br />
for LAN/WANs utilization studies. Assists with network design changes/enhancements for improved<br />
system availability and performance.<br />
(3) Education and Other Requirements. A Bachelor of Science or Masters of Science degree from an<br />
accredited college or university with a major in Computer Science, Information <strong>Systems</strong>, Engineering<br />
or other related scientific or technical discipline.<br />
a) Substitution. Four (4) to seven (7) years direct network experience, Bachelor of Science or<br />
Bachelor of Arts degree from an accredited college or university with a major in a non-technical<br />
discipline. Demonstrated system-level network aptitude based upon experience.<br />
B6: Junior <strong>Systems</strong> Engineer<br />
(1) Experience Requirements:<br />
a) Total Experience. One (1) to three (3) years of progressive specific experience in planning,<br />
designing and analyzing telecommunications networks. This experience must include familiarity<br />
with Ethernet, FDDI, frame relay and ATM, and a working knowledge of operating systems and<br />
protocols such as Novell, NT, UNIX, SNA and TCP/IP. Must be familiar with PCs in a client<br />
server environment.<br />
(2) Functional Responsibility. Assists in the design and implementation of LAN/WANs using hub<br />
and router technology. Performs hardware/software analyses to provide comparative data of<br />
performance characteristics and suitability within the existing systems environment. Assists with<br />
changes/enhancements for improved system availability and performance.<br />
(3) Education and other requirement. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering or other related<br />
scientific or technical discipline.
(a) Substitution. Two (2) to four (4) years direct network experience, Bachelor of Science or<br />
Bachelor of Arts degree from an accredited college or university with a major in a non-technical<br />
discipline. Demonstrated system-level network aptitude based upon experience.<br />
B7: Sustaining Engineer<br />
(1) Experience Requirements:<br />
(a) Total Experience. Three (3) or more years of intensive and progressive specific experience in<br />
planning, supporting and analyzing telecommunication networks. This experience must include<br />
demonstrated knowledge of network data transport protocols such as Ethernet, frame relay and<br />
ATM, and a working knowledge of operating systems and protocols such as Novell, NT, UNIX,<br />
SNA, and TCP/IP. Must have practical experience with network management tools.<br />
(2) Functional Responsibility. Assists in the design and implementation of LAN/WANs using hub and<br />
router technology. Performs hardware/software analyses to provide comparative data of performance<br />
characteristics and suitability within the existing systems environment. Prepares trade-off studies and<br />
evaluations for vendor equipment. Directly involved with network monitoring and performance data<br />
collection and presentation for LAN/WANs utilization studies. Recommends network design<br />
changes/enhancements for improved system availability and performance.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering or other related<br />
scientific or technical discipline.<br />
(a) Substitution. Four (4) or more years experience and less than a Bachelor of Science or<br />
Bachelor of Arts degree completed in a technical or non-technical discipline. Proven ability to<br />
work effectively individually or as part of a project team. Experience as a project leader is a plus.<br />
B8: Junior Sustaining Engineer<br />
(1) Experience Requirements:<br />
One (1) to three (3) years direct network experience<br />
(2) Functional Responsibility. Duties are performed under the direct guidance of a senior engineer, or<br />
project manager. Assists in the design and implementation of LAN/WANs using hub and router<br />
technology. Performs hardware/software analyses to provide comparative data of performance<br />
characteristics and suitability within the existing systems environment. Directly involved with<br />
network monitoring and performance data collection and presentation. Assists with network design<br />
changes/enhancements for improved system availability and performance. Generally involved with<br />
maintenance and control of a network, and its management center.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in a non-technical discipline<br />
(a) Substitution. Two (2) to four (4) years experience and less than a Bachelor of Science or<br />
Bachelor of Arts degree completed in a technical or non-technical discipline<br />
B9: Senior Sales Engineer<br />
(1) Experience Requirements:
a) Total Experience. Seven (7) or more years of intensive and progressive specific experience in<br />
planning, designing and analyzing telecommunications networks. This experience must include<br />
demonstrated knowledge of legacy network protocols, as well as knowledge of Ethernet, FDDI,<br />
frame relay and ATM, and a working knowledge of operating systems and protocols such as NT,<br />
UNIX, SNA and TCP/IP. Must have experience with network analysis/management techniques<br />
and be familiar with PCs in a client server environment. Must be familiar with IT and long<br />
distance and local carrier management. Highest skills in written and oral communication.<br />
Experience as a supervisor or task leader essential. Knowledge of computer languages is a plus.<br />
(b) Task Leader. Indicates this category may serve as a task leader on one or more task orders.<br />
Management experience will be required since the category qualifications do not require<br />
managerial experience. Task leaders must have supervisory or project leader experience. This<br />
experience is not in addition to the experience requirements for the skill category. Project leader<br />
experience is experience that demonstrated an individual’s ability to accomplish projects/tasks<br />
through others.<br />
(2) Functional Responsibility. Responsible for direct or indirect involvement in the design and<br />
implementation of LAN/WANs using hub and router technology. Performs hardware/software<br />
analyses to provide comparative data of performance characteristics and suitability within the existing<br />
systems environment. Prepares trade-off studies and evaluations for vendor equipment. Recommends<br />
network design changes/enhancements for improved system availability and performance.<br />
(3) Education and Other Requirements. A Bachelor of Science or Masters of Science degree from an<br />
accredited college or university with a major in Computer Science, Information <strong>Systems</strong>, Engineering<br />
or other related scientific or technical discipline.<br />
(a) Substitution. Ten (10) or more years direct network experience, minimum of Bachelor of<br />
Science or Bachelor of Arts degree from an accredited college or university with a major in a nontechnical<br />
discipline. Demonstrated system-level network aptitude based upon experience. Proven<br />
high aptitude for technical and project leadership. Proven ability to work effectively individually<br />
or as part of a project team.<br />
B10: Sales Engineer<br />
(1) Experience Requirements:<br />
a) Total Experience. Five (5) to eight (8) years of intensive and progressive specific experience in<br />
planning, designing and analyzing telecommunications networks. This experience must include<br />
demonstrated knowledge of legacy network protocols, as well as knowledge of Ethernet, FDDI,<br />
frame relay and ATM, and a working knowledge of operating systems and protocols such NT,<br />
UNIX, SNA and TCP/IP. Must be familiar with PCs in a client server environment. Highest<br />
demonstrated skills in written and oral communications. Experience as a supervisor or task leader<br />
essential. Knowledge of computer languages is a plus.<br />
b) Task Leader. Indicates this category may serve as a task leader on one or more task orders.<br />
Management experience will be required since the category qualifications do not require<br />
managerial experience. Task leaders must have supervisory or project leader experience. This<br />
experience is not in addition to the experience requirements for the skill category. Project leader<br />
experience is experience that demonstrates an individual’s ability to accomplish projects/tasks<br />
through others.<br />
(2) Functional Responsibility. Responsible for direct or indirect involvement in the design and<br />
implementation of LAN/WANs using hub and router technology. Performs hardware/software
analyses to provide comparative data of performance characteristics and suitability within the existing<br />
systems environment. Prepares trade-off studies and evaluations for vendor equipment. Recommends<br />
network design changes/enhancements for improved system availability and performance.<br />
(3) Education and Other Requirements. A Bachelor of Science or Masters of Science degree from an<br />
accredited college or university with a major in Computer Science, Information <strong>Systems</strong>, Engineering<br />
or other related scientific or technical discipline.<br />
a) Substitution. Eight (8) or more years direct network experience, Bachelor of Science or<br />
Bachelor of Arts degree from an accredited college or university with a major in a non-technical<br />
discipline. Demonstrated system-level network aptitude based upon experience. Proven high<br />
aptitude for technical and project leadership. Proven ability to work effectively individually or as<br />
part of a project team.<br />
B11: <strong>Network</strong> Security Project Manager<br />
(1) Experience Requirements:<br />
a) Total Experience. Ten (10) years of technical management in the area of network security.<br />
b) Specialized Experience. Four (4) years of specialized experience in the area of designing and<br />
implementing network security architectures in support of both legacy and distributed topologies<br />
(2) Functional Responsibility. Provides direct supervision and management to a team of network<br />
security engineers and analysts with respect to deliverable execution. Responsible for program<br />
management based on work break down structures to accomplish specific network security tasks.<br />
Must be familiar with Microsoft Project and Excel.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business or other related disciplines<br />
a) Substitution. Education may be substituted by an additional two (2) years of experience for each<br />
year of education requirement<br />
B12: <strong>Network</strong> Security Senior Consultant<br />
(1) Experience Requirements.<br />
a) Total Experience. Six (6) years of network security consulting<br />
(b) Specialized Experience. Four (4) years of specialized network security experience in the areas<br />
of PKI, VPN and firewall engineering<br />
(2) Functional Responsibility. Advises customer on procedures and processes on PKI and VPN related<br />
issues in support of distributed architectures based on customer’s network security requirements.<br />
Familiar with firewall installations, configurations, and implementations in support of the customer.<br />
Assists customer with design and implementation of secure network architectures. Familiar with<br />
network security COTS based products.<br />
(3) Education and Other Requirements. A Masters of Science degree from an accredited college or<br />
university with a major in Computer Science, Business or other related disciplines.<br />
a) Substitution. Substitution not allowed for this category.<br />
B13: Senior <strong>Network</strong> Security Engineer
(1) Experience Requirements:<br />
(a) Total Experience. Six (6) years of network security experience.<br />
b) Specialized Experience. Four (4) years of specialized in the area of PKI, VPN and firewall<br />
engineering<br />
(2) Functional Responsibility. Serves as a senior engineer on a team that is responsible for providing<br />
secure solutions in both legacy and distributed environments. Must have hands-on experience with<br />
developing and implementing VPNs using PKI COTS based products. Experienced with conducting<br />
network security test and evaluation processes leading up to certification and accreditation on<br />
distributed networks. Understands and is familiar with the installation, configuration and<br />
implementation of various COTS based firewalls.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business, or other related disciplines<br />
(a) Substitution. Substitution not allowed for this category<br />
B14: <strong>Network</strong> Security Engineer<br />
(1) Experience Requirements:<br />
(a) Total Experience. Four (4) years of network security experience<br />
(b) Specialized Experience. Two (2) years of specialized in the area of firewall engineering and<br />
PKI<br />
(2) Functional Responsibility. Serves as an engineer on a team that is responsible for providing secure<br />
solutions in both legacy and distributed environments. Must have hands-on experience with<br />
developing and implementing firewalls using COTS based products. Experienced with conducting<br />
network security test and evaluation processes leading up to certification and accreditation on<br />
distributed networks. Understands and is familiar with the installation, configuration and<br />
implementation of various PKI encryption products.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business, or other related disciplines.<br />
(a) Substitution. Substitution not allowed for this category.<br />
B15: Junior <strong>Network</strong> Security Engineer<br />
(1) Experience Requirements:<br />
(a) Total Experience. Two (2) years of network security experience.<br />
(2) Functional Responsibility. Serves as a junior engineer on a network security team that is<br />
responsible for providing secure solutions in both legacy and distributed environments. Must have<br />
hands-on experience with developing and implementing firewalls and access control applications,<br />
including MLS, using COTS based products. Some experience with conducting network security test<br />
and evaluation processes leading up to certification and accreditation on distributed networks.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business, or other related disciplines
(a) Substitution. Education may be substituted by an additional 2 years of experience for each<br />
year of education requirement<br />
B16: Senior <strong>Network</strong> Security Analyst<br />
(1) Experience Requirements:<br />
(a) Total Experience. Six (6) years of network security experience<br />
(b) Specialized Experience. Four (4) years of specialized in the area of <strong>Network</strong> Security Policy,<br />
including certification and accreditation processes<br />
(2) Functional Responsibility. Serves as a senior analyst on a team that is responsible for providing<br />
secure solutions in both legacy and distributed environments. Must have hands-on experience with<br />
developing and implementing network security policy and procedure. Working knowledge of<br />
certification and accreditation processes of critical applications in support of both legacy and<br />
distributed network architectures. Familiar with OMB A-130 and DITSCAP requirements<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business, or other related disciplines.<br />
(a) Substitution. Substitution not allowed for this category<br />
B17: <strong>Network</strong> Security Analyst<br />
(1) Experience Requirements:<br />
(a) Total Experience. Four (4) years of network security experience.<br />
(b) Specialized Experience. Two (2) years of specialized in the area of <strong>Network</strong> Security Policy,<br />
including certification and accreditation processes.<br />
(2) Functional Responsibility: Serves as an analyst on a network security team that is responsible for<br />
providing secure solutions in both legacy and distributed environments. Must have hands-on<br />
experience with developing and implementing network security policy and procedure. Working<br />
knowledge of certification and accreditation processes of critical applications in support of both legacy<br />
and distributed network architectures. Familiar with OMB A-130 and DITSCAP requirements<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business or other related disciplines.<br />
(a) Substitution. Substitution not allowed for this category<br />
B18: Junior <strong>Network</strong> Security Analyst<br />
(1) Experience Requirements:<br />
a) Total Experience. Two (2) years of network security experience.<br />
(2) Functional Responsibility. Serves as an analyst on a network security team that is responsible for<br />
providing secure solutions in both legacy and distributed environments. Some hands-on experience<br />
with developing and implementing network security policy and procedure<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Business or other related disciplines.
(a) Substitution. Education may be substituted by an additional 2 years of experience for each year<br />
of education requirement<br />
B19: Senior Technical Writer (<strong>Network</strong> Security)<br />
(1) Experience Requirements:<br />
(a) Total Experience. Five (5) years of technical writing or documentation experience<br />
(b) Specialized Experience. Three (3) years of specialized network security oriented technical<br />
documentation experience.<br />
(2) Functional Responsibility. Prepares and edits network security IT/ADP documentation<br />
incorporating information provided by user, specialist, analyst, programmer, and operations personnel.<br />
Must have a substantial knowledge of the capabilities of network security. Duties include writing,<br />
editing, and graphic presentation of technical information for both technical and non-technical<br />
personnel. Interprets technical documentation standards and prepares documentation according to<br />
standards. Must be capable of working independently. Plans and supervises multiple projects and/or<br />
tasks involving a wide wide-range of IT network security related tasks.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in English, Computer Science, Business or other related disciplines.<br />
a) Substitution. Substitution not allowed for this category<br />
B20: Technical Writer (<strong>Network</strong> Security)<br />
(1) Experience Requirements:<br />
(a) Total Experience. Three (3) years of network security technical writing or documentation<br />
experience<br />
(b) Specialized Experience. One (1) year of specialized network security technical documentation<br />
experience<br />
(2) Functional Responsibility. Prepares and edits network security IT/ADP documentation<br />
incorporating information provided by user, specialist, analyst, programmer, and operations personnel.<br />
Must have a substantial knowledge of the capabilities of network security in support of information<br />
systems. Duties include writing, editing, and graphic presentation of technical information for both<br />
technical and non-technical personnel. Interprets technical network security documentation standards<br />
and prepares documentation according to standards. Must be capable of working independently. This<br />
category provides incidental support for other approved requirements.<br />
(3) Education and Other Requirements. An Associate's degree from an accredited college or university<br />
or two (2) years of college or university study in English, Computer Science or related discipline.<br />
(a) Substitution. Substitution not allowed for this category<br />
B21. <strong>Network</strong> Manager<br />
(1) Experience Requirements:
(a) Total Experience. Five (5) years experience in one or more of the following areas: data<br />
communications engineering, data communications hardware or software analysis, network<br />
administration or management, or data communication equipment installation and maintenance.<br />
(b) Task Leader. Indicates this category may serve as a task leader on one or more task orders.<br />
Management experience will be required since the category qualifications do not require<br />
managerial experience. Task leaders must have supervisory or project leader experience. This<br />
experience is not in addition to the experience requirements for the skill category. Project leader<br />
experience is experience that demonstrates an individual's ability to accomplish projects/tasks<br />
through others.<br />
(2) Functional Responsibility. Performs a variety of network management functions in support of MIS<br />
services related to the operation, performance or availability of data communications networks.<br />
Modifies command language programs, network start up files, assigns/re-assigns network device<br />
logicals, analyzes network performance and recommends adjustments to wide variety of complex<br />
network management functions with responsibility for overall performance and availability of<br />
networks. LAN/WAN consultant skilled in network analysis, integration and tuning. Experience with<br />
cable/LAN meters, protocol analyzers, SNMP and RMON based software products. Knowledge of<br />
Ethernet, FDDI and high speed WAN's and routers. Analyze client LAN's/WAN's, isolate source of<br />
problems, recommend reconfiguration and implementation of new network hardware to increase<br />
performance. Working knowledge of network operating systems. Modifies command language<br />
programs, network start up files, assigns/re-assigns network device logicals. Conducts load balancing<br />
efforts to achieve optimum device utilization and network performance. Manages network E-mail<br />
functions. Establishes mail boxes and monitors mail performance on the network. Coordinates with<br />
engineering groups to resolve hardware problems. Works with customer and operations staff in<br />
scheduling preventative and emergency maintenance activities. May serve as task leader on one or<br />
more task orders.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information Technology, Engineering, or a related<br />
discipline. If applicable, shall be certified as a network engineer for the specific network operating<br />
system as defined in the Government task request. The certification criteria are determined by the<br />
network operating system vendor.<br />
(a) Substitution. Substitution not allowed for this category.<br />
B22. <strong>Network</strong> Administrator<br />
(1) Experience Requirements.<br />
(a) Total Experience. Three (3) years experience in one or more of the following areas: data<br />
communications engineering, data communications hardware or software analysis, network<br />
administration or management, data communication equipment installation and maintenance, or<br />
computer systems administration and management.<br />
(2) Functional Responsibility. Performs a variety of network management functions related to the<br />
operation, performance or availability of data communications networks. Experience with cable/LAN<br />
meters, protocol analyzers, SNMP and RMON based software products. Knowledge of Ethernet, FDDI<br />
and high speed WAN's and routers. Analyze client LAN's/WAN's, isolate source of problems,<br />
recommend reconfiguration and implementation of new network hardware to increase performance.<br />
Working knowledge of network operating systems. Modifies command language programs, network<br />
start up files, assigns/re-assigns network device logicals, participates in load balancing efforts<br />
throughout the network to achieve optimum device utilization and performance. Establishes new user<br />
accounts on the network granting access to required network files and programs. Manages network E-<br />
mail functions. Establishes mail boxes and monitors mail performance on the network. Troubleshoots
network/user problems, presents resolutions for implementation. Prepares a variety of network<br />
resource reports.<br />
(3) Education and Other Requirements. An Associate's degree from an accredited college or<br />
university in a related field, or two (2) years of college or university study in a related field. If<br />
applicable, should be certified as a network administrator for a specific network operating system as<br />
defined in the Government task request. Certification criteria are determined by the network operating<br />
system vendor.<br />
C. RESERVED<br />
a) Substitution. Substitution not allowed for this category<br />
D. COMPUTER OPERATIONS SERIES (D1-D6)<br />
D1. Reserved<br />
D2. Computer <strong>Systems</strong> Analyst<br />
(1) Experience requirements.<br />
(a) Total Experience. Three (3) years progressive experience in the analysis and design of business<br />
or scientific applications using database management systems or high-order programming<br />
languages.<br />
(2) Functional Responsibility. Performs systems analysis, design, programming, documentation, or<br />
implementation of complex system applications and related IT/ADP systems concepts for effective<br />
implementation. Participates in all phases of the software development life cycle with emphasis on the<br />
planning, analysis, programming, testing and acceptance phases. Designs and prepares technical<br />
reports and related documentation, and makes charts and graphs to record results. Prepares and delivers<br />
presentations and briefings as required.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering, or other related<br />
scientific or technical discipline.<br />
(a) Substitution. Substitution not allowed for this category<br />
D3. Applications Engineer<br />
(1) Experience requirements.<br />
(a) Total Experience. Eight (8) years of progressive in managing or performing software<br />
engineering activities.<br />
(b) Specialized Experience. Six (6) years of specific experience working with C++, SQL, and<br />
third/fourth generation languages in the design and implementation of systems and using database<br />
management systems. General experience includes increasing responsibilities in software<br />
engineering activities. Knowledgeable of applicable standards.<br />
(2) Functional Responsibility. Analyzes and studies complex system requirements. Designs software<br />
tools and subsystems to support software reuse and domain analyses and manages their<br />
implementation. Manages software development and support using formal specifications, data flow<br />
diagrams, other accepted design techniques and Computer Aided Software Engineering (CASE) tools.<br />
Estimates software development costs and schedule. Reviews existing programs and assists in making
efinements, reducing operating time, and improving current techniques. Supervises software<br />
configuration management.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in Computer Science, Information <strong>Systems</strong>, Engineering, Business or other<br />
related scientific or technical discipline.<br />
(a) Substitution:<br />
– With a Master degree (in the fields described in section b above): six (6) years general<br />
experience of which at least four (4) years specialized experience is required<br />
– With eleven (11) years of general experience of which at least nine (9) years of specialized<br />
experience, a degree is not required<br />
D4. Operations Manager<br />
(1) Experience: Seven years experience, of which at least give years must be specialized. Specialized<br />
experience includes: supervision and operation experience on a large-scale computer system,<br />
knowledge of hardware, software and operating systems. General experience includes operations<br />
experience on a large scale computer system or a multi-server local area network.<br />
(2) Functional Responsibility: Manages computer operations. Ensures production schedules are met.<br />
Ensures computer system resources are used effectively. Coordinates the resolution of production<br />
related problems. Ensures proper relationships are established between customers, teaming partners,<br />
and vendors to facilitate the delivery of information technology services. Provides users with<br />
computer output. Supervises staff operations.<br />
(3) Educational Requirement(s): A Bachelor's degree in Computer Science, Information <strong>Systems</strong>,<br />
Engineering, Business, or other related discipline.<br />
D5. Reserved<br />
- With a Master's degree (in the fields described in above): five (5) years general experience of<br />
which at least three (3) years must be specialized experience is required<br />
- With ten years of general experience of which at lest eight (8) years must be specialized<br />
experience, a degree is not required<br />
D6. <strong>Systems</strong> operator<br />
(1) Experience: Minimum of three years experience, of which at least two years must be specialized<br />
experience operating a large-scale computer system or a multi-server local area network. Must<br />
demonstrate sufficient knowledge of programming to understand how programs use computer<br />
hardware.<br />
(2) Functional Responsibility: Monitors and supports computer processing. Coordinates input, output,<br />
and file media. Distributes output and controls computer operation which may be mainframe, mini, or<br />
client/server based.<br />
(3) Educational Requirement(s): An Associate's degree in Computer Science, Information <strong>Systems</strong>,<br />
Engineering, Business, or other related discipline is required.<br />
-- With a Bachelor's degree (in the fields described above): two (2) years general experience of<br />
which at least one (1) year must be specialized experience is required
-- With seven (7) years general experience of which at least five (5) years is specialized, a degree<br />
is not required.<br />
E. Technician Series (E1-E2)<br />
E1. RESERVED<br />
E2. Communications Technician<br />
(1) Experience Requirements:<br />
(a) Total Experience. Three (3) years experience installing and maintaining communications and<br />
cable systems. Experience should include termination of voice and data circuits including copper<br />
and fiber house wiring.<br />
(2) Functional Responsibility. Responds to help calls referred by the Help Desk or Customer Support.<br />
Implements, installs, and repairs voice and data cable systems. Creates and maintains records on cable<br />
assignments, terminations and directory headings, telephone, circuit, and other communication<br />
equipment types.<br />
(3) Education and Other Requirements.<br />
(a) A high school diploma<br />
(b) Two (2) years technical school training related field<br />
(c) Substitution. Substitution not allowed for this category<br />
F. Support Series (F1-F6)<br />
F1: SENIOR TECHNICAL WRITER<br />
(1) Experience Requirements.<br />
(a) Total Experience. Five (5) years of technical writing or documentation experience<br />
(b) Specialized Experience. Three (3) years of specialized IT oriented technical documentation<br />
experience<br />
(2) Functional Responsibility. Prepares and edits IT/ADP documentation incorporating information<br />
provided by user, specialist, analyst, programmer, and operations personnel. Must have a substantial<br />
knowledge of the capabilities of computer systems. Duties include writing, editing, and graphic<br />
presentation of technical information for both technical and non-technical personnel. Interprets<br />
technical documentation standards and prepares documentation according to standards. Must be<br />
capable of working independently. Plans and supervises multiple projects and/or tasks involving a<br />
wide range of IT related tasks.<br />
(3) Education and Other Requirements. A Bachelor of Science degree from an accredited college or<br />
university with a major in English, Computer Science, Business, or other related disciplines.<br />
F2. Tech Writer<br />
(a) Substitution. Substitution not allowed for this category.
(1) Experience Requirements:<br />
(a) Total Experience. Three (3) years of technical writing or documentation experience<br />
(b) Specialized Experience. One (1) year of specialized ADP technical documentation experience<br />
(2) Functional Responsibility. Prepares and edits IT/ADP documentation incorporating information<br />
provided by user, specialist, analyst, programmer, and operations personnel. Must have a substantial<br />
knowledge of the capabilities of computer systems. Duties include writing, editing, and graphic<br />
presentation of technical information for both technical and non-technical personnel. Interprets<br />
technical documentation standards and prepares documentation according to standards. Must be<br />
capable of working independently. This category provides incidental support for other approved<br />
requirements.<br />
(3) Education and Other Requirements. An Associate's degree from an accredited college or university<br />
or two (2) years of college or university study in English, Computer Science or related discipline<br />
(a) Substitution. Substitution not allowed for this category<br />
F3. Administrative Support/Graphics Specialist<br />
(1) Experience: At a minimum, one years of specialized experience using commercial automated word<br />
processing (e.g. MS Word, WordPerfect), graphics systems (Harvard, Freelance, PowerPoint, etc.) and<br />
desktop publishing systems. Demonstrated ability to work independently or under only general<br />
direction.<br />
(2) Functional Responsibility: Directly supports Program Manager or Project Manager by maintaining<br />
personnel and other files; prepares correspondence, schedules and coordinates travel. Assists in the<br />
preparation of presentation graphics and supports the development of contract deliverables and reports<br />
by developing and updating graphic presentations to improve the quality and enhance the usability of<br />
these documents. Responsible for integrating the graphics generated with automated tools and the<br />
deliverable documents.<br />
(3) Education: High school diploma and a minimum of two years experience in office administration<br />
and developing graphic/artistic presentations for publications and documents (preferably technical<br />
documentation).<br />
F4. Help Desk Manager<br />
(1) Experience: Minimum of seven years experience. Of which at least five years must be specialized.<br />
Specialized experience includes: management of help desks in a multi-server environment,<br />
comprehensive knowledge of PC operating systems, E.g. DOS, Windows, NT, as well as networking<br />
and mail standards and supervision of help desk employees. General experience includes information<br />
systems development, network and other work in the client/server field, or related fields.<br />
Demonstrated ability to communicate orally in writing and a positive customer service attitude.<br />
(2) Functional Responsibility: Provides daily supervision and direction to staff who are responsible for<br />
phone and in-person support to users in the areas of e-mail, directories, standard Windows desktop<br />
applications, and applications developed or deployed under a particular contract. These personnel<br />
serve at the second point of contact for trouble shooting hardware/software, PC, printer and network<br />
problems<br />
(3) Education: Bachelor's degree in Computer Science, Information <strong>Systems</strong>, Engineering, Business<br />
or other related discipline
-- With a Master's degree (in the fields described above): five years general experience of which<br />
at least three years must be specialized experience is required<br />
-- With ten years general experience of which at least eight years is specialized, a degree is not<br />
required<br />
F5. HELP DESK SPECIALIST<br />
(1) Experience: Minimum of five years experience, of which at least three years must be specialized.<br />
Specialized experience includes; knowledge of PC operating systems, e.g., DOS, Windows, NT, as<br />
well as networking and mail standards and work on a help desk. General experience includes<br />
information systems development and other work in the client/server field, or related fields.<br />
Demonstrated ability to communicate orally and in writing and a positive customer service attitude.<br />
(2) Functional Responsibility: Provides phone and in-person support to users in the areas of e-mail,<br />
directories, standard Windows desktop application, and applications developed under this contract or<br />
predecessors. Serves as the initial point of contact for troubleshooting hardware/software, PC, printer,<br />
and network problems.<br />
(3) Education: An Associate's degree in Computer Science, Information <strong>Systems</strong>, Engineering,<br />
Business, or other related discipline is required.<br />
-- With a Bachelor's degree (in the fields described above): four years general experience of which<br />
at least two years must be specialized experience is required<br />
-- With eight years general experience of which at least six years is specialized, a degree is not<br />
required<br />
F6. TECHNICAL TYPIST<br />
(1) Experience Requirements:<br />
(a) Total Experience. One (1) year of technical typing<br />
(2) Functional Responsibility. Prepares draft and final form technical documents. Must be capable of<br />
typing at average or above average speed. Must be capable of typing technical narratives and data.<br />
Responsible for spelling, grammar, and proper format, and for proofreading finished documents. Must<br />
be capable of using various word processing equipment. This category provides incidental support for<br />
other approved requirements.<br />
(3) Education and Other Requirements. High School diploma<br />
(a) Substitution. Substitution not allowed for this category
<strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong> (FNS)<br />
Contract Number: GS-35F-0440N<br />
GSA Group 70 Schedule Pricing Base Year: March 25, 2003 - March 24, 2004<br />
FNS Facility Base Year Year 2 Year 3 Year 4 Year 5<br />
Management (A1 – A3)<br />
A1. Program Manager $203.71 $211.04 $218.64 $226.51 $234.67<br />
A2. Project Manager $169.15 $175.24 $181.55 $188.08 $194.85<br />
A3. Project Administrator $62.15 $64.39 $66.71 $69.11 $71.59<br />
[A4 through A14 Reserved]<br />
Technology (A15 – A23)<br />
A15. Chief Technologist $297.20 $307.90 $318.98 $330.47 $342.36<br />
A16. Principal Technologist $228.13 $236.34 $244.85 $253.67 $262.80<br />
A17. Divisional Technologist $201.48 $208.73 $216.25 $224.03 $232.10<br />
A18. Senior Technical Professional $171.12 $177.28 $183.66 $190.27 $197.12<br />
A19. Technical Professional $152.80 $158.30 $164.00 $169.90 $176.02<br />
A20. Staff Technical Professional $115.49 $119.65 $123.95 $128.42 $133.04<br />
A21. Senior Project Administrator $95.63 $99.07 $102.64 $106.33 $110.16<br />
A22. Senior Data Control Specialist $90.41 $93.66 $97.04 $100.53 $104.15<br />
B. NETWORK SERIES(B1-B24)<br />
B1. Senior <strong>Network</strong> Engineer $141.42 $146.51 $151.79 $157.25 $162.91<br />
B2. <strong>Network</strong> Engineer $118.67 $122.94 $127.37 $131.95 $136.70<br />
B3. Junior <strong>Network</strong> Engineer $84.60 $87.65 $90.80 $94.07 $97.46<br />
B4. Senior <strong>Systems</strong> Engineer $138.14 $143.11 $148.27 $153.60 $159.13<br />
B5. <strong>Systems</strong> Engineer $124.36 $128.84 $133.48 $138.28 $143.26<br />
B6. Junior <strong>Systems</strong> Engineer $104.69 $108.46 $112.36 $116.41 $120.60<br />
B7. Sustaining Engineer $124.36 $128.84 $133.48 $138.28 $143.26<br />
B8. Junior Sustaining Engineer $113.45 $117.53 $121.77 $126.15 $130.69<br />
B9. Senior Sales Engineer $169.15 $175.24 $181.55 $188.08 $194.85<br />
B10. Sales Engineer $152.80 $158.30 $164.00 $169.90 $176.02<br />
B11. <strong>Network</strong> Security Project Manager $152.80 $158.30 $164.00 $169.90 $176.02<br />
B12. <strong>Network</strong> Security Senior Consultant $171.12 $177.28 $183.66 $190.27 $197.12<br />
B13. Senior <strong>Network</strong> Security Engineer $141.42 $146.51 $151.79 $157.25 $162.91<br />
B14. <strong>Network</strong> Security Engineer $124.36 $128.84 $133.48 $138.28 $143.26<br />
B15. Junior <strong>Network</strong> Security Engineer $113.45 $117.53 $121.77 $126.15 $130.69<br />
B16. Senior <strong>Network</strong> Security Analyst $152.80 $158.30 $164.00 $169.90 $176.02<br />
B17. <strong>Network</strong> Security Analyst $113.45 $117.53 $121.77 $126.15 $130.69<br />
B18. Junior <strong>Network</strong> Security Analyst $90.41 $93.66 $97.04 $100.53 $104.15<br />
B19. Senior Technical Writer, <strong>Network</strong> Security $113.45 $117.53 $121.77 $126.15 $130.69<br />
B20. Technical Writer, <strong>Network</strong> Security $90.41 $93.66 $97.04 $100.53 $104.15<br />
B21 RESERVED<br />
B22. RESERVED<br />
D. Computer Operations Series (D1-D7)<br />
D1. RESERVED<br />
D2. RESERVED
D3 Applications Engineer $124.36 $128.84 $133.48 $138.28 $143.26<br />
D4. RESERVED<br />
D6 RESERVED<br />
E. Technician Series (E1.-E2)<br />
E1. RESERVED<br />
E2. Communications Technician $90.41 $93.66 $97.04 $100.53 $104.15<br />
F. Support Series (F1-F6)<br />
F3. Administrative Support/Graphics Specialist $49.59 $51.38 $53.22 $55.14 $57.13<br />
F4. RESERVED<br />
F5. RESERVED<br />
F6. Technical Typist $49.59 $51.38 $53.22 $55.14 $57.13
<strong>Federal</strong> <strong>Network</strong> <strong>Systems</strong> <strong>LLC</strong> (FNS)<br />
Contract Number: GS-35F-0440N<br />
GSA Group 70 Schedule Pricing Base Year: March 25, 2003 - March 24, 2004<br />
Customer Facility Base Year Year 2 Year 3 Year 4 Year 5<br />
Management (A1 – A3)<br />
A1. Program Manager $145.04 $150.26 $155.67 $161.27 $167.08<br />
A2. Project Manager $118.30 $122.55 $126.97 $131.54 $136.27<br />
A3. Project Administrator $56.07 $58.08 $60.17 $62.34 $64.59<br />
[A4 through A14 Reserved]<br />
Technology (A15 – A23)<br />
A15. RESERVED<br />
A16. Principal Technologist $159.55 $165.30 $171.25 $177.41 $183.80<br />
A17. RESERVED<br />
A18. Senior Technical Professional $101.99 $105.66 $109.47 $113.41 $117.49<br />
A19. Technical Professional $96.36 $99.83 $103.43 $107.15 $111.01<br />
A20. Staff Technical Professional $73.32 $75.96 $78.70 $81.53 $84.47<br />
A21. RESERVED<br />
A22. Senior Data Control Specialist $53.37 $55.29 $57.28 $59.34 $61.48<br />
B. NETWORK SERIES(B1-B24)<br />
B1. Senior <strong>Network</strong> Engineer $98.89 $102.45 $106.14 $109.96 $113.92<br />
B2. <strong>Network</strong> Engineer $86.97 $90.10 $93.35 $96.71 $100.19<br />
B3. Junior <strong>Network</strong> Engineer $49.42 $51.19 $53.04 $54.95 $56.93<br />
B4. Senior <strong>Systems</strong> Engineer $92.92 $96.26 $99.73 $103.32 $107.04<br />
B5. <strong>Systems</strong> Engineer $86.97 $90.10 $93.35 $96.71 $100.19<br />
B6. Junior <strong>Systems</strong> Engineer $56.34 $58.37 $60.47 $62.65 $64.90<br />
B7. Sustaining Engineer $86.97 $90.10 $93.35 $96.71 $100.19<br />
B8. Junior Sustaining Engineer $79.33 $82.18 $85.14 $88.21 $91.38<br />
B9. RESERVED<br />
B10. RESERVED<br />
B11. <strong>Network</strong> Security Project Manager $91.31 $94.59 $98.00 $101.53 $105.18<br />
B12. RESERVED<br />
B13. Senior <strong>Network</strong> Security Engineer $98.89 $102.45 $106.14 $109.96 $113.92<br />
B14. <strong>Network</strong> Security Engineer $86.97 $90.10 $93.35 $96.71 $100.19<br />
B15. Junior <strong>Network</strong> Security Engineer $74.11 $76.78 $79.55 $82.41 $85.38<br />
B16. Senior <strong>Network</strong> Security Analyst $106.87 $110.72 $114.70 $118.83 $123.11<br />
B17. <strong>Network</strong> Security Analyst $79.33 $82.18 $85.14 $88.21 $91.38<br />
B18. Junior <strong>Network</strong> Security Analyst $63.24 $65.52 $67.88 $70.32 $72.85<br />
B19. RESERVED<br />
B20. Technical Writer, <strong>Network</strong> Security $42.03 $43.54 $45.11 $46.73 $48.42<br />
B21 <strong>Network</strong> Manager $103.62 $107.35 $111.22 $115.22 $119.37<br />
B22. <strong>Network</strong> Administrator $56.07 $58.08 $60.17 $62.34 $64.59<br />
D. Computer Operations Series (D1-D7)<br />
D1. RESERVED<br />
D2. Computer <strong>Systems</strong> Analyst $79.33 $82.18 $85.14 $88.21 $91.38
D3 Applications Engineer $86.97 $90.10 $93.35 $96.71 $100.19<br />
D4. Operations Manager $103.62 $107.35 $111.22 $115.22 $119.37<br />
D6. <strong>Systems</strong> Operator $56.07 $58.08 $60.17 $62.34 $64.59<br />
E. Technician Series (E1.-E2)<br />
E1. RESERVED<br />
E2. RESERVED<br />
F. Support Series (F1-F6)<br />
F1. RESERVED<br />
F2. RESERVED<br />
F3. RESERVED<br />
F4. Help Desk Manager $103.62 $107.35 $111.22 $115.22 $119.37<br />
F5. Help Desk Specialist $56.07 $58.08 $60.17 $62.34 $64.59<br />
F6. RESERVED