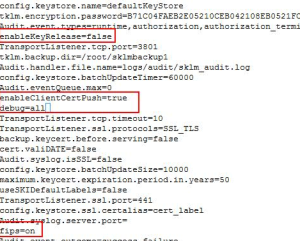
Step 2.Validate the below entries populated in SKLMConfig.properties, else manually fill in
cat /opt/IBM/WebSphere/AppServer/products/sklm/config/SKLMConfig.properties
Step 3.Restart ISKLM server. Once the restart completes,you should be able to see SSL protocol, KMIP protocol status as “configured”. Restarting sklm server(Navigate to the /opt/IBM/WebSphere/AppServer//bin directory)
./stopServer.sh server1 -username <username> -password <password>
./startServer.sh server1 -username <username> -password <password>
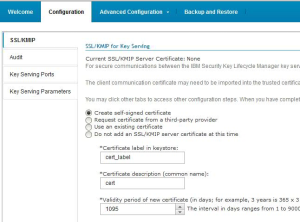
Step 4.Validate whether the created self-signed certificate is configured properly and is in-use
Step 5.Export the configured / in-use server certificate as a file, following tklmCertList and tklmCertExport CLI commands.This file can be transferred to tape for ssl communication.
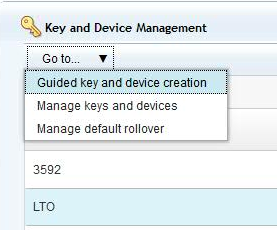
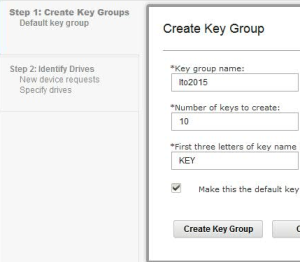
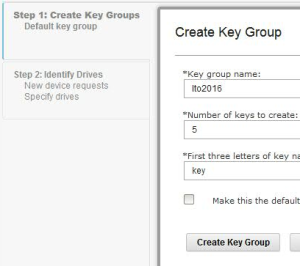
Step 6.Create Keys associated to the device group LTO
Note: Two key groups created to manage default rollover
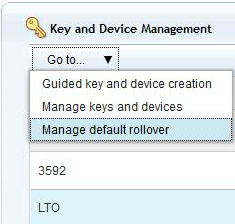
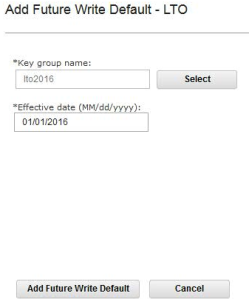
Step 7:Manage key rollover
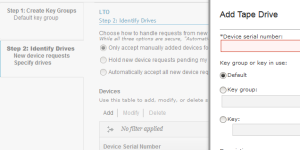
Step 8. Identify drives to manually add devices(drives) ,otherwise it automatically accept all new device requests for communication if step 9 is followed before 8.
Step 9.On tape library web – manage library -> logical library -> select library ->modify encryption method
Enter your EKM primary address and tcp port number in that page.
To test configuration
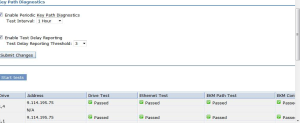
1.Tape library web – Service library->key path diagnostics ->start tests
This confirms your sklm server got well configured with tape for encryption.